SaaS Security - Office 365 Email - User Reported Phishing
Email users are key in fighting against phishing. Users can help detect missed attacks, let the security administrators remediate the detected attacks, and adjust the policies to prevent similar attacks in the future.
Avanan automatically ingests these reports, alerts administrators about them, and presents them in a dedicated dashboard. This allows administrators to investigate and take necessary actions.
Benefits
- Present potentially missed attacks in the Avanan console.
- Integrated solution for the security admins to investigate and take actions.
- Simple, powerful way to increase end-users involvement and interact with them.
User Reported Phishing Dashboard
The user reported phishing dashboard allows to view the phishing reports made by the end-users.
Whenever a user marks an email as suspected phishing, a new entry is created in the dashboard, and the administrator can review it and perform the relevant actions.
To see the user reported phishing emails, navigate to User Interaction > User Reported Phishing.
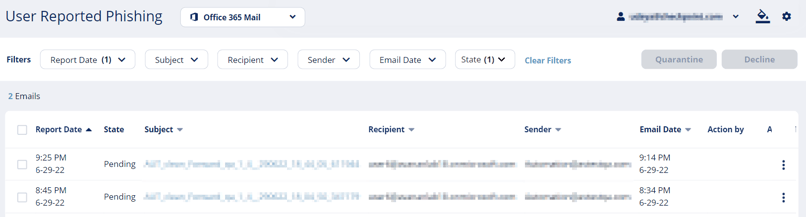
Acting on Phishing Reports
Administrators can perform one of these actions on phishing reports:
- Decline - The report will be declined as the reported email does not seem to be malicious. The email remains in the user's mailbox.
- Quarantine - The report will be approved and the email will be sent to quarantine.
- Block-list/Allow-list rule - The administrator will choose to create an Anti-Phishing Exceptions.
Notifying End Users about Approving/Declining their Reports
Administrators can choose to notify end users whenever their phishing reports are approved or declined. To enable these notifications:
-
Go to Security Settings > User Interaction > Phishing Reports.
-
In the User-Reported Phishing Emails section, select the Notify users when their reports are approved/declined checkbox.
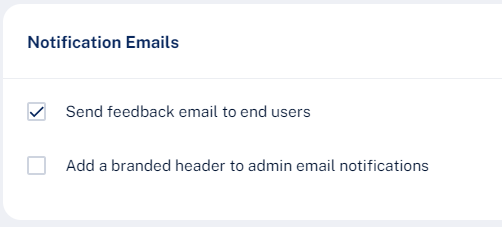
-
Scroll down and select Save and Apply.
Note - This will also enable end user notifications for rejected quarantine restore requests.
To configure the notification subject and body:
- Go to Security Settings > SaaS Applications.
- To configure the templates for Office 365 Mail, click Configure for Office 365 Mail.
- To configure the templates for Gmail, click Configure for Gmail.
- Scroll-down to Advanced and edit these templates:
- Phishing report decline:
- Report Phishing decline subject
- Report Phishing decline body
- Phishing report approve:
-
- Report Phishing approve subject
- Report Phishing approve body
- Report Phishing approve subject
-
- Phishing report decline:
Automatic Ingestion of End User Reports
Note - For integration with a third party solution, contact Avanan Support.
Dedicated Phishing Reporting Mailboxes
Some organizations provide one or more dedicated mailboxes to end-users to forward phishing emails to (for example, phishing_reports@mycompany.com). You can configure Avanan to scan such mailboxes, add every email forwarded to them to the User Reported Phishing dashboard and create a user-reported phishing event.
To add dedicated mailboxes to the User Reported Phishing dashboard:
- Navigate to Security Settings > User Interaction > Phishing Reports.
- Select the Dedicated phishing reporting mailboxes checkbox.
- Enter the required mailbox email address.
Note - To add multiple mailboxes, enter the mailbox addresses separated by a comma.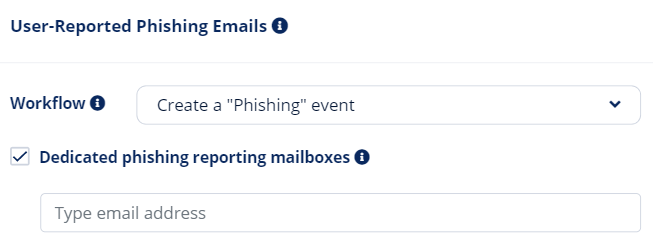
- Click Save and Apply.
Note - All emails sent by protected users to these mailboxes generate events for administrators to review in the User Reported Phishing dashboard. Make sure these are dedicated mailboxes to report phishing.
Generating Events for User Reported Phishing
When a user reports a phishing email, the administrators can determine the event type to be generated by
the Avanan.
The available options are:
- Create an "Alert" event
- Create a "Phishing" event
- Do nothing
To configure event type for the User Reported Phishing emails:
- Navigate to Security Settings > User Interaction > Phishing Reports.
- In the User-Reported Phishing Emails section, in Workflow, select the event type to be generated.
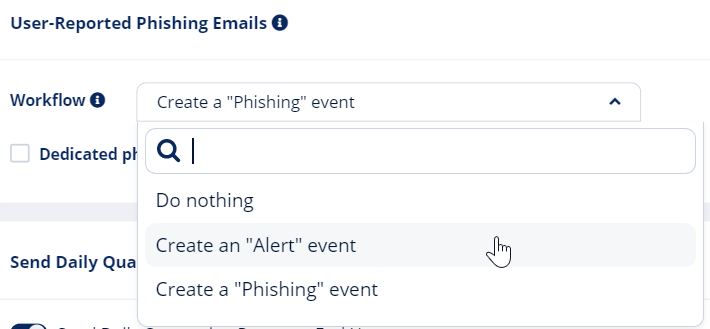
- Click Save and Apply.
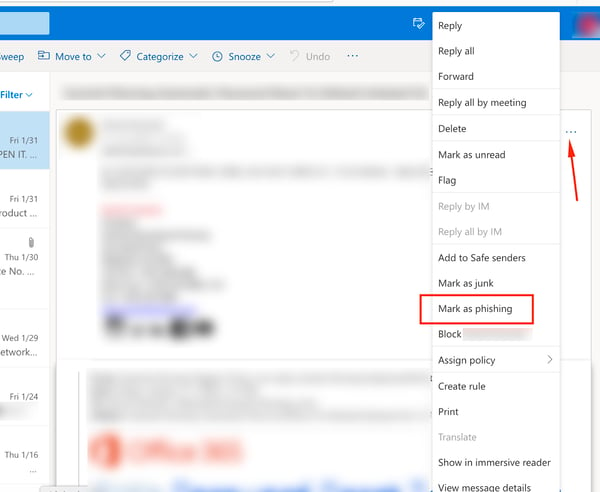
Microsoft Report Message Add-in
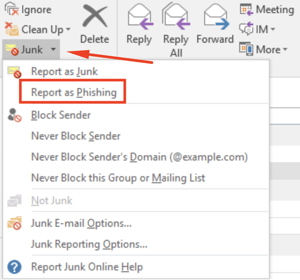
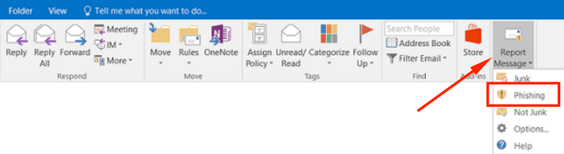
Microsoft offers a built-in Mark as Phishing option in Outlook. When a user clicks this option, Microsoft gets notified of the missed suspected phishing email and sends a reports to phish@office365.microsoft.com.
Avanan integrates with the native Report Message add-in for Microsoft 365. When a user reports an email as phishing, Avanan immediately shows the email in the User Reported Phishing dashboard and creates a user-reported phishing event.
Enable Email as Phishing Option in Outlook
By default, in Outlook, the ability to report an email as phishing is enabled.
Office 365 administrators can add the Report Message add-in to their users’ desktop clients if it is not already enabled. To enable the Report Message add-in, refer to Microsoft documentation.
Report Phishing Email from Outlook
Web Client
Desktop Client