The ability to search through clean and malicious messages quickly, based on multiple criteria and remove them from the inbox as necessary is an essential part of the admin's job.
When you see an attack on the horizon, the best and most important thing to do is to stop it across all mailboxes, even across all customers.
To do so, security teams need to figure out where the smoking gun lies in a phishing event that may have resulted in a breach. Getting a list of all the emails from a particular sender or domain with a specific subject is critical. Just as critical is being able to get those emails out of the inbox with one click.
To do so, Avanan has a powerful and easy-to-use "Search and Destroy" feature, within Mail Explorer. It allows you to search for all emails that Avanan is aware of. Deep integrations into MS365 and G-Suite allow us to search inboxes for the criteria you define. You can search by sender IP, header—whatever you want. You can locate messages that even arrived seconds earlier. This allows admins to look at email details, including email headers and bodies, and quarantine if necessary.
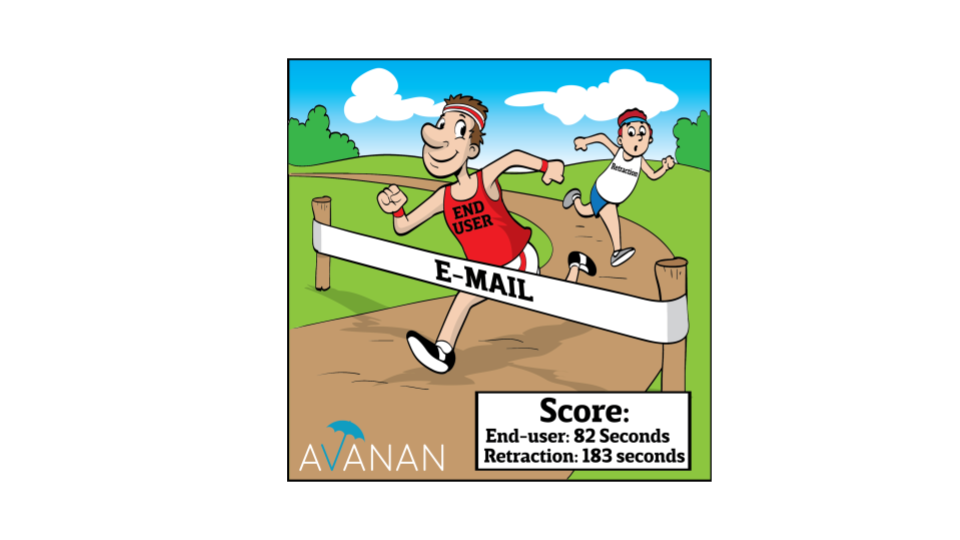
With Search and Destroy, admins can effectively claw back all those messages from the user inbox in one click. You can also create a block list to prevent similar deliveries. It allows to instantly remove known threats from inboxes. It allows for bulk quarantining, with a custom query engine.
It's scalable to quarantine email across the enterprise in seconds.
It works as a great post-delivery forensics tool, as you're able to pull all malicious files from the entire environment in a few clicks.
It can even stop the dreaded reply-all email chain storms, as an admin can search for the initial sender and subject of the original email, and create a policy to move, delete or edit all emails in the chain.
And through our Mail Explorer, being able to see what's caught and why is valuable information for admins.
Manual remediation is never glamorous. But Mail Explorer makes it easy—and maybe even a little fun.
Knowing the threats and being able to respond to them is key. With Search and Destroy, it's easier than ever.
Watch the video below for a detailed tutorial: