A new report confirms what has long been assumed: Microsoft Office is now the most targeted platform for hackers.
In 2019, more than 70% of all attacks targeted Microsoft Office. In 2017, that number was 16%. That's a dramatic 337.5% increase. And you can imagine that that will only increase.
One of the main reasons for the shift is the speed in which cybercriminals respond to changes in security. New vulnerabilities are discovered and exploits are sold as dark-web wares before Microsoft has a chance to respond.
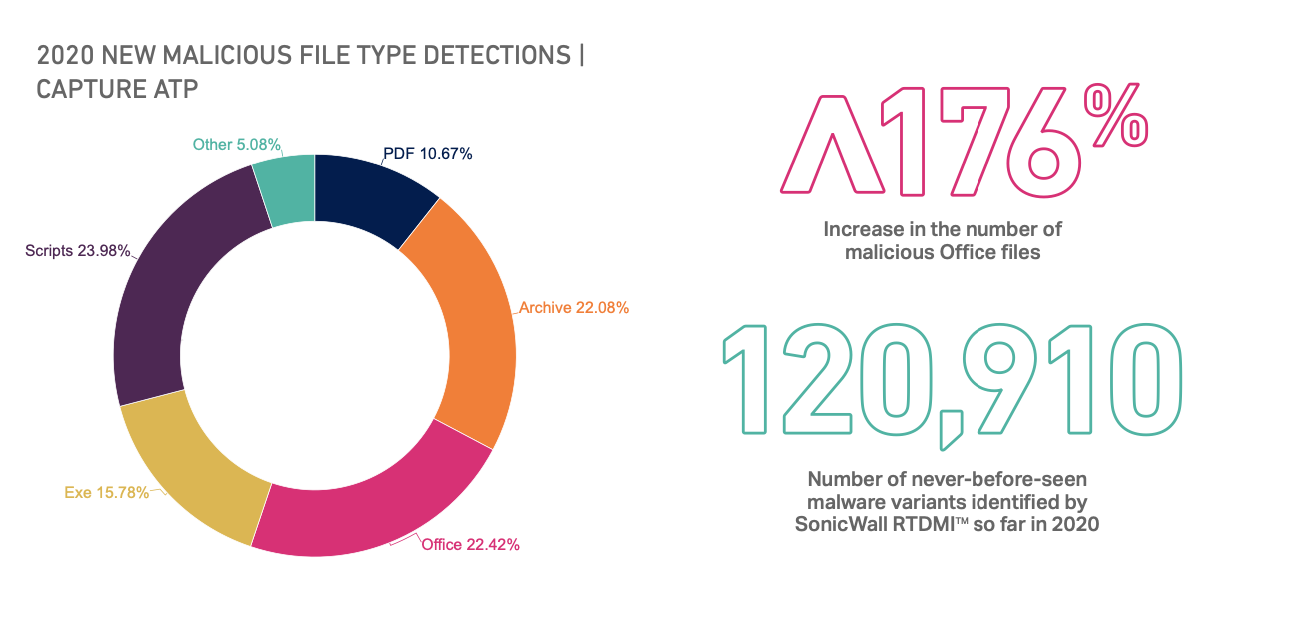
Not only is Microsoft 365 the most-targeted cloud, Microsoft document files have replaced Adobe PDF as the most preferred malware vector. According to a new report from SonicWall, Office documents account for 22.4% of malicious files, as compared to 10.7% for PDFs.
Because Office 365 is the most popularly-used platform for email—it has more than double the amount of email messages than G-Suite— hackers are going to spend their energy and resources trying to get past it. Recently, we wrote about how hackers have expanded the battleground from email to web in order to bypass Microsoft Safe Links.
As we found last year in the 2019 Global Phish Report, 1 in 4 attacks bypass Microsoft's default EOP defenses and as discussed in our 2020 Microsoft ATP Report, 1 in 10 malicious email bypass Microsoft Advanced Threat Protection. Targeted campaigns can often lead to miss rates as high as 78%.
With Office being targeted more and more every day, you need the security that it's specifically trained to block them.