This week’s Data Connectors Cybersecurity Strategies Conference in Fort Lauderdale was a special occasion. Klint Walker, the Chief Information Security Advisor (CISA) for the US Department of Homeland Security, led a keynote session on the state of security and how it can be improved.
To get the Florida audience interested, he posed a question that hit close to home. “Everyone here preps for hurricane season, right? Raise your hand if you do.” Hundreds of hands flew up. “What about malware season? When is that?” Someone in the front shouted out “All year round, baby!”
They're right. Just like cleaning a house, security is a never ending responsibility. And it’s not just mom’s responsibility. It’s everyone’s responsibility. Klint elaborated:
“Cybersecurity is everyone's responsibility. Let’s be clear: it’s not IT’s responsibility. Your IT shop manages the program and risk. It is up to everyone in the organization to actually follow the program. One person could put you on the front page of a newspaper or put you out of business.”

Then, he posed another question to the audience. 3% of people in the room raised their hands in response to “How many of you trust that your employees are using different passwords than their Netflix account?” In their defense, passwords are hard to remember. Apparently, so is the fact that password managers and MFA exist to solve that problem.
That person who puts your company out of business after an embarrassing security breach could also be a partner. Take the Kevin Bacon attack as an example. Klint explained, going deep into the hacker mindset: "I don’t attack the company I want to attack. I attack the company seven degrees away. You don’t think companies merging together are vulnerable?” Makes sense, right? (Avanan covered a similar attack during the summer, when hackers breached the Salesforce account of a trusted partner to send them phishing emails.)
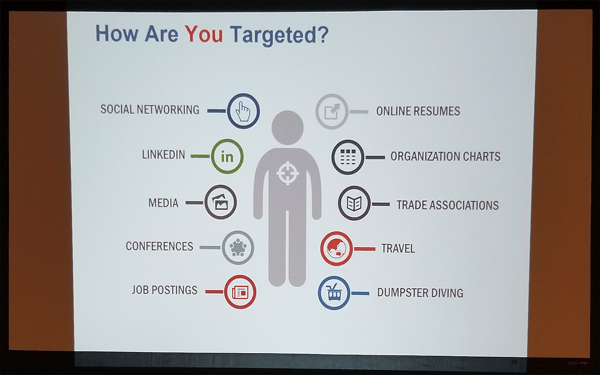
That’s the very definition of social engineering. In the image above from Klint's keynote session, you can see the various tactics hackers use to learn about their victims. The bad guys trick people who you trust to get into the front door, gaining legitimate access through convincing spoofs that seem standard and sincere. Even less convincing phishing emails with a non-business bend get clicks. Bad guys use popular topics — like news on impeachment hearings or the latest crazy cat video — to craft phishing emails that people want to open so they don’t miss out on the latest news. Fear of missing out is powerful.
It’s a security truism that no solution can prevent breaches at a rate of 100%. The idea that one of your users’ accounts is compromised is a less popular mindset. But every security professional should be making this assumption, argues Avanan Chief Privacy Officer, Michael Landewe. He explained that “We live in a society without perimeters. That's why over 87GB of email addresses and passwords have already been exposed and are online for hackers to use. The philosophy that a compromise has already happened should guide your security decisions to ensure that you make the right ones.” (Get the details of his presentation "How Hackers Bypass Office 365 Security" here.)
Ever since security has moved away from the data center, the attack chain has too. The attack chain is now cloud->cloud->cloud. The target isn’t your desktop anymore; it’s your cloud services. And your security isn’t the last line of defense: it’s your users.
Make password security and mindful link clicking a job responsibility. Put it in your job descriptions. When security stops being IT’s responsibility, and everyone’s job, it will be less of a problem, saving you money and time down the line.
About Data Connectors
Since 1999, Data Connectors has brought together security professionals interested in compliance and cybersecurity, and the vendors using machine learning and AI to make this possible. The confluence of local business representatives and community leaders fosters important dialogue on the direction of cybersecurity.
The Ft. Lauderdale event took place on November 14th, 2019. Avanan is a sponsor and presenter at several Data Connectors Cybersecurity events.