What’s more dangerous than hackers running amok in your corporate email? How about if they had global access to your salesforce.com account?
Salesforce.com [$CRM] is used by more than 150,000 organizations, boasting over 3.75M users around the globe, making it the world’s most widely used CRM system. The cloud software enables a host of capabilities for customer management, including the ability to generate invoices. These invoices are sent as an email from the Salesforce servers, but with the company domain as the sender. Millions of invoices are sent monthly, coming in as trusted senders and processed without a second thought.
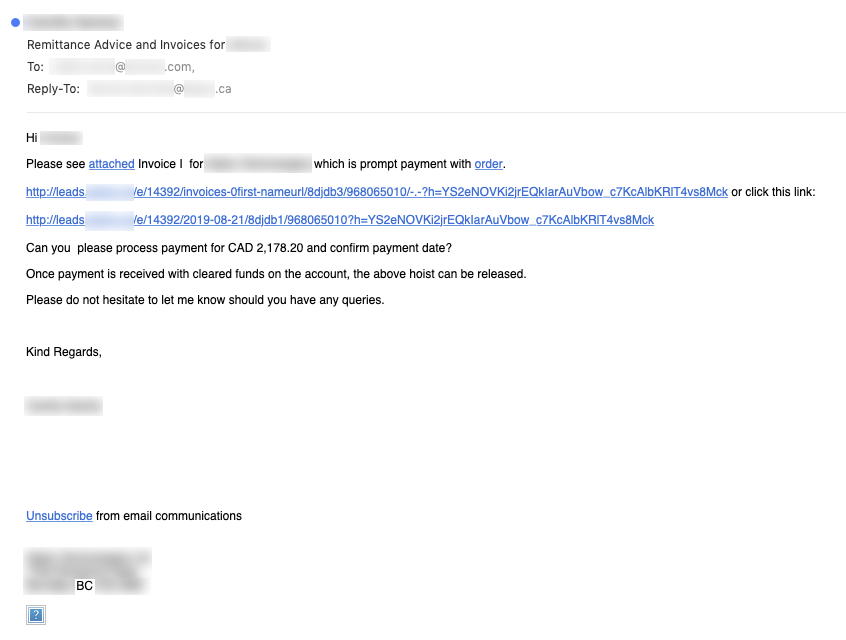
Avanan recently uncovered a phishing attack that was using Salesforce's invoice-sending functionality against one of our customers (a Fortune 500 company). Hackers compromised one of their vendors' Salesforce account to send the customer phishing emails with fake invoices. Because these fake invoices replicated the patterns of legitimate invoices, they were almost untraceable by the security layers of Office 365.
For the sending organization (our customer's vendor) that had their Salesforce account compromised, this is a devastating exposure. Not only was all their sensitive data exposed, including that of customers and partners, but the breach also inflicted immeasurable damage to their corporate reputation.
Salesforce Attack - How The Scam Works
In the attack, hackers compromised a Salesforce account to utilize Email Studio — a tool in the Salesforce.com ecosystem that enables users to build and send personalized email communications — to coordinate a massive invoice phishing attack against partners and customers.
Avanan's analysis of the attack also revealed that the hackers managed to compromise the public website of the sender’s company and inject two malicious URL paths. The phishing scam (coming from Salesforce - a legitimate source) contained links that were pointing to what looked like the company's legitimate website.
Salesforce Phishing Attack in 5 Steps
Step 1
Hackers compromise an organization’s Salesforce account and public website.
Step 2
Hackers inject malicious code into the partner’s website to generate two public-facing URLs.
Step 3
Within Salesforce, the hackers access Email Studio, draft emails containing the URLs they created in Step 2, and send them to contacts stored in Salesforce.
Step 4
The victim organization receives the phishing emails sent in Step 3
Step 5
The victim clicks on the URL, which points to a page with malware.
In the example we analyzed, 1,056 people in the company received the email.
In the example we analyzed, the hackers goal was to install a trojan malware on the endpoints with URLs that pointed to pages that start downloading malware. The same scam could apply to fake invoices or credential harvesting pages.
Indicators of Compromise (IOCs)
|
URL Path |
e/14392/invoices-0first-nameurl/8djdb3/968065010/-.-?h=YS2eNOVKi2jrEQkIarAuVbow_c7KcAlbKRlT4vs8Mck |
|
URL Path |
e/14932/2019-08-21/8djdb1/968065010?h=YS2eNOVKi2jrEQklarAuVbow_c7KcAlbKRlT4vs8Mck |
The email was flagged as suspicious by the Avanan platform, and upon further inspection, the client organization informed Avanan Security Researchers for further review.
In this case, the hackers were lazy. Had they waited, and learned the normal paths of communications, they could have sent even more targeted invoices that matched standard payment cycles and were sent to the appropriate person. A diligent network of hackers could perform better analysis to make the activity look less suspicious.
Immediate Recommendations
We advise that you:
- Enable MFA on your CRM so you don’t become the sender of such emails
- Add an advanced security layer to your email, to filter emails based on the more advanced algorithm than what the default security provides
- Add a Mail Security Orchestration Automation and Response platform (M-SOAR) to quickly eliminate such attacks in case they make it through
- Define the approval process for invoices to protect from fake invoices
- Train employees on the concept of zero trust and adopt a Continuous Adaptive Risk and Trust-Based Approach (CARTA) to manage the risks of digital business and strengthen security strategy.
Summary
This attack is particularly difficult to detect because the victim frequently receives legitimate invoices from the same Salesforce account that was breached. Moreover, the message, links, and sender were not spoofed; they legitimately came from Salesforce and pointed to the organization’s legitimate public website.
For these reasons, the email could have easily been interpreted as a false positive by security solutions. Additionally, Salesforce communications originate from trusted infrastructure that’s generally regarded to be a safe source when scanned by security products.
SalesPharce can be more dangerous than Business Email Compromise (BEC). Even your trusted partner can betray you, whether they do it maliciously or they get hacked.