The State of Business Email Compromise
Everyone is talking about Business Email Compromise (BEC) attacks. And with good reason.
Gartner has found that BECs increased by nearly 100% in 2019 and through 2023, they predict that BEC attacks will continue to double each year, at a cost of over $5 billion to its victims.
The payment for a BEC attack nearly doubled between the first and second quarter of 2020, now at an average cost of $80,183.
It's no wonder, then, that people are on guard more than ever. And it's no wonder that people have questions about business email compromise scams.
How do they work? Why are they so successful? And how can you stop them?
We'll go over everything you need to know to guard against BEC attacks.
Business Email Compromise Definition
The end goal of every BEC is to get the recipient to do something that they shouldn't. Wire money; give over credentials; share sensitive information. All of these are things that benefit the hacker.
It starts by identifying a victim. Hackers will do tons of research to not only learn about the victim, but also the rest of the company they work for. That means understanding who the CEO or CFO is, and even beyond that.
From there, they will compromise an account. This could be done in many ways. The goal is to get control of the email account for someone in a leadership position.
The hacker will then target their victim with a specific request, usually in the form of an urgent appeal for money or data.
Business Email Compromise Examples
It affects organizations of all sizes, in all industries, and it victimizes executives and regular employees alike. BEC has fooled Google and Facebook for $100 Million and a small church in Ohio for $1.8 Million. Sequoia Capital was breached via a BEC. It's hard to avoid these days.
Here's an example of what it looks like in the wild.
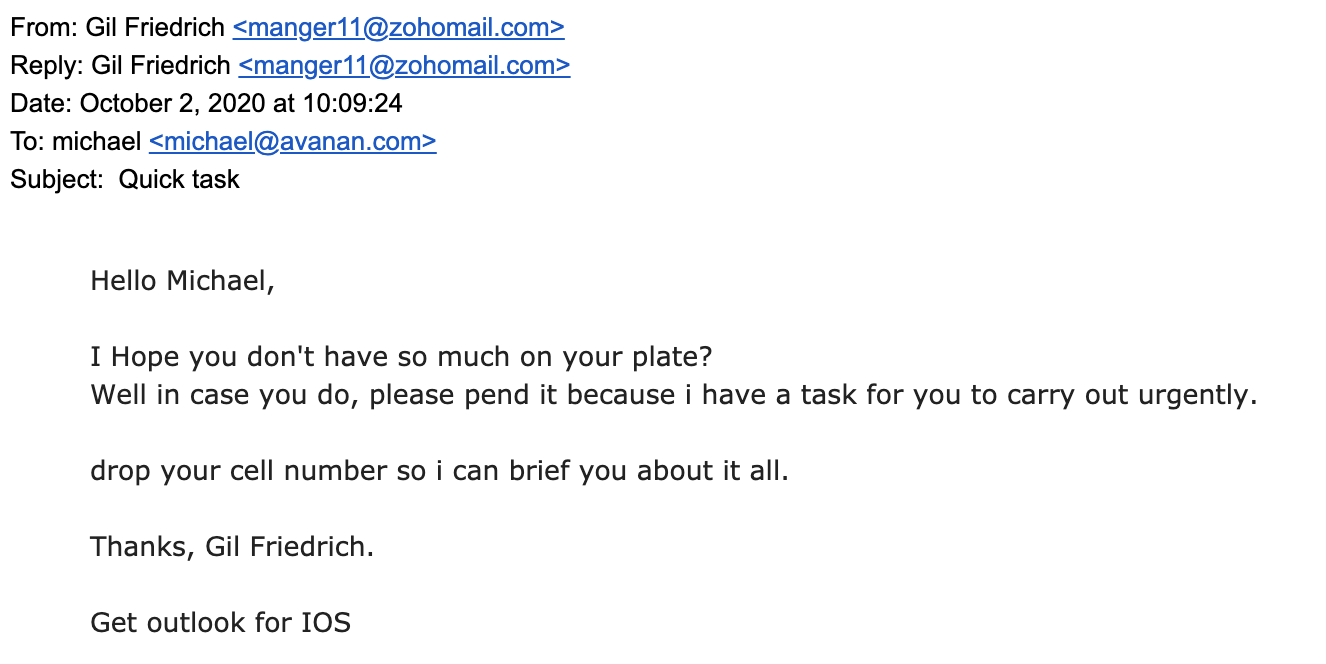
This was sent from our "CEO" Gil Friedrich, to our lead threat hunter Michael Landewe.
Knowing it was fake—grammatical errors everywhere, plus it's not Gil's actual email—we decided to play along to see what the hackers wanted. Using a Google Voice account, here's what the conversation looked like:
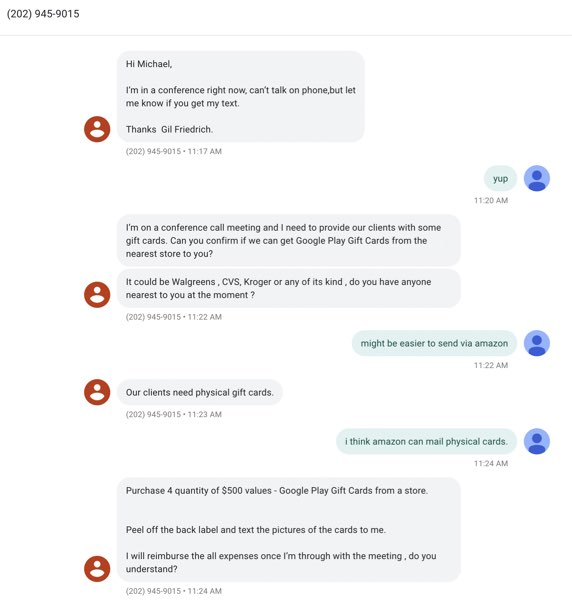
So, our "Gil" wanted $2,000 worth of gift cards. And was not thrilled with the idea of getting gift cards from somewhere other than a store. Why's that? Scammers don't like virtual cards because they can be traced back. Physical cards however, or at least the photo of the code, can be sold for fifty cents on the dollar on the dark web.
Gift card BEC scams are actually quite popular. The Internet Crime Complaint Center tracked a 1,240% increase in 2018 of these types of attacks. And at the beginning of the COVID-19 pandemic, scammers were asking victims to buy gift cards to help purchase PPE.
Using urgency from a higher-up can easily fool a junior employee to do something they shouldn't. The three most popular keywords in a BEC email are urgent, request, and important. All are used in an attempt to create a mix of fear and subservience in the victim.
And it's working.
Business Email Compromise Prevention
BECs are hard to stop because you need internal context to know that one is occurring. Companies like Mimecast and Proofpoint are designed only to monitor inbound email—therefore they have no way of scanning internal email or understanding the context or conversational relationships within an organization. When an SEG sees an email from the 'CEO' to the 'CFO', it will be the first time it has seen such a conversation. It won't know, then, if a "gift card" is a common request or something out of the ordinary.
Both Microsoft and Google have the internal access required to prevent BEC attacks and many of their anti-spoofing tools do a good job at blocking basic attacks. But the issue is that their infrastructure cannot perform the per-customer contextual analysis required for most BEC attacks.
They work with far too many companies and customers to properly monitor all internal accounts and understand an organization's relationship and reputation patterns.
Here's what's needed to truly guard against BECs.
- Machine learning algorithms combine with role-based, contextual analysis of previous conversations to identify threats that Google, Microsoft and external mail gateways miss,
- Deployment-day analysis of one-year's email conversations to build trusted reputation network,
- Scanning and quarantine of internal email and files in real-time, protecting against east-west attacks and insider threats,
- AI and machine learning techniques to rapidly adapt to new threats and behaviors,
- Account takeover protection beyond email: login events, configuration changes and end user activities throughout the suite.
Business Email Compromise Solutions
Business email compromise attacks are scary. They are on the rise and they can do grave financial damage to an organization.
Companies, though, are not completely defenseless. A solution that leverages internal context, AI and a trusted reputation network unique to a company can thwart these attacks.