When 2-factor authentication (2FA) is combined with password managers like 1Password and LastPass, it can help people securely access their personal and work accounts, and make it more difficult for hackers to breach private data. But those taking advantage 2FA often use the most insecure version of it — such as email and SMS-based codes that hackers can acquire with ease.
Multi-Factor Authentication (MFA) security raises the barrier to account access by requiring another proof of identity (usually in the form of an alphanumeric code), but it does not stop phishing. Specifically, MFA does nothing to stop Business Email Compromise (BEC), Account Takeover, and social engineering emails impersonating executives to extract financial gain.
The most and least secure forms of MFA
People who take advantage of multi-factor authentication often use the most insecure options, such as email and SMS-based codes that hackers can acquire with ease. In this way, the MFA space is fraught with loopholes for hackers to exploit.
There are many forms of MFA to take advantage of, but it’s important to know that some types of MFA are more secure than others. Below, I rank MFA from least secure to most secure.
5. Email code (most insecure)
For email-based MFA, the account provider sends the user a 5-10 digit alphanumeric token via email that they then input into the login page, after they’ve already input their username and password. This method of MFA does not stop phishing if this user’s account is already compromised, but they don’t know it.
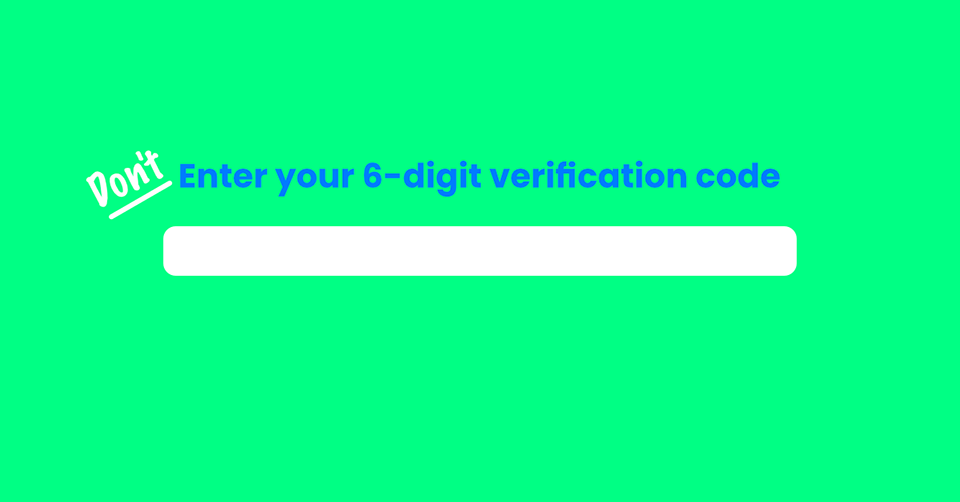
4. Phone-based authentication (code sent via SMS or phone call)
Because cell phones are always on our person, online account providers use text messages and phone calls as another factor of authentication. Though convenient, this method of MFA security can be intercepted. The simplest way that hackers can interfere with this authentication process is to direct the user to a spoofed login page that forwards the phone-based MFA code to the hacker.
Spoofed login pages are particularly effective on mobile phones. Because the screens are smaller than laptops, details on the webpage that indicate an impersonation are less noticeable. According to page 14 of this year’s Verizon Data Breach Investigation Report, “Research points to users being significantly more susceptible to social attacks they receive on mobile devices.”
There are other ways hackers use your cell phone against you. After visiting your social media accounts, they could have enough information to convince an AT&T or Verizon representative to transfer your SIM card or phone number to their device. This is called “SIM swapping.” Usually, hackers would only put in this effort if the target was a public figure and there was large sums of money to be gained. Slightly more unlikely but still possible, hackers can use another vector to install malware in the cell phone and forward text message-based authentication codes to their device.
3. Authenticator apps
Phone-based apps like Google Authenticator continually generate one-time passwords that expire at frequent intervals. These time-based codes constantly rotate through the app, regardless of if the user needs them or not.
Authenticator apps are not password protected, however. The codes generated in the app are tied to the device itself, rather than the user’s online identity. While it would be very rare for a hacker to take possession of their target’s phone, it is possible for someone to discover a cell phone with a weak password (like 1234) and use their authenticator app to gain access to online accounts — especially if they use Google’s password manager, which loads credentials without requiring credentials.
2. Security keys (also known as universal 2nd factor)
Hardware-based Yubikeys and other universal 2nd factor devices are a physical rebuttal to the ethereality of the cloud, where data can be remotely accessed. Users plug these “keys” into computers like USBs, and then tap them with their finger to authenticate the application they’re trying to access. (The tap doesn’t scan for fingerprints; it’s just part of the product’s tactility.) Like magic links sent to email accounts, these hardware keys are considered a form of passwordless authentication.
Many customers experience issues with their hardware key, which is why Gmail, for example, provides backup methods of authentication in the event that they’re having trouble getting the key to work. Hardware keys are only ideal when the user configures their account so that other account recovery options are not available at login.
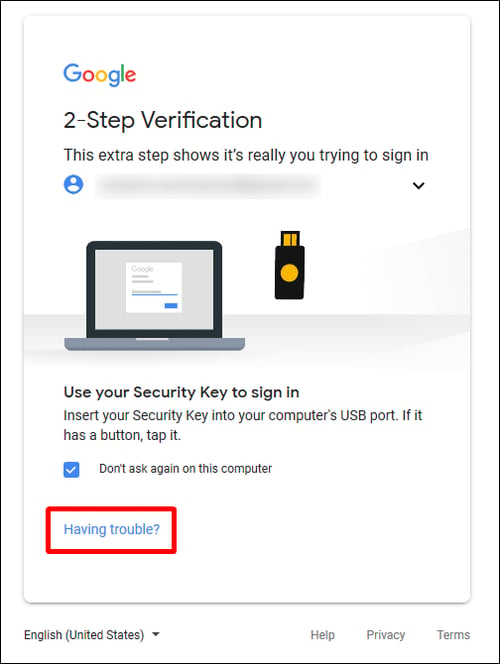
Hardware-based authentication tokens (shown in the image above) are touted as the most difficult to bypass form of 2FA, but most SaaS accounts offer users alternative options in case they experience difficulties.
1. Biometrics (most secure)
Currently, there is no widespread implementation of biometric-based MFA on commercially available devices, despite the fact that most smartphones can capture biometrics. Like hardware-based keys, the physical aspect of this authentication method makes it difficult for hackers to interfere with this extremely personalized login process. Once biometric MFA becomes compatible with popular SaaS applications, it will be the most bulletproof form of MFA.
When MFA doesn’t help
Multi-factor authentication is another form of perimeter security, but the cloud has no perimeter. People often think that because they have MFA, they’re immune to phishing attacks. To be clear, MFA is not designed to stop attacks not related to logins. It only secures online accounts at the perimeter, when the user logs in to gain access.
Here are some scenarios where MFA security can not stop phishing:
- Spoofed login pages
- Impersonation attacks
- CEO fraud
- BEC
- Fraudulent requests for the transfer of funds or W-2s
- Embedded links to malware
Make sure everyone at your organization has MFA, and knows about out-of-band authentication.
Everyone should have multi-factor authentication. It is the bare minimum of security. Without MFA, the rest of your security is irrelevant — especially in Office 365 and G Suite.
In order to protect online accounts, users should do two things. First, they should rely on password managers to generate complicated passwords that they don’t even have to remember. Secondly, they should ensure that the most secure forms of MFA are running on their accounts. Finally, they should use out-of-band authentication whenever applicable. When your users receive a suspicious request for the transfer of funds, for example, we recommend they call the person who emailed them to confirm the request. By removing the process from online channels, they diverge from the path the hacker has guided them along and can see that they’re being phished.
Multi-factor authentication security should not be trusted as the final line of defense for authentication, even though it currently is. The immediate challenge is fortifying the MFA infrastructure so that fewer loopholes exist, and educating people using MFA on these loopholes.