Recently, we've seen a lot of news about Quishing--or QR Code phishing. This is when the link behind a QR code is malicious, but the QR code itself is not. There was a report of a major U.S. energy firm targeted by a QR phishing code. Other reports have noticed an uptick in these types of attacks.
In fact, Harmony Email researchers have found that nearly all of our customers have been targeted with a QR code-based attack. That coincides with a 587% increase in QR code attacks from August to September.
Why are these trending upward? They seem innocuous enough, just those friendly QR codes that we use to scan menus.
But they are a great way to hide malicious intent. The image can hide a malicious link and if the original image isn’t scanned and parsed, it’ll appear as just a regular image.
And because end-users are accustomed to scanning QR codes, getting one in an email isn’t necessarily a cause for concern.
In this attack brief, Harmony Email researchers will discuss how hackers are utilizing QR codes to obtain credentials.
Attack
In this attack, hackers are using QR codes to hide malicious links.
- Vector: Email
- Type: Credential Harvesting, Quishing
- Techniques: Social Engineering
- Target: Any end-user
Email Example
It’s very easy to create a QR code. There are tons of free sites that make it super simple to do.
QR codes go to a link. Hackers—or anyone else—can put anything in that link for the QR code to redirect to.
In this attack, hackers have created a QR code that goes to a credential harvesting page. The lure is that the Microsoft MFA is expiring, and you need to re-authenticate.
Though the body says it comes from Microsoft security, the sender's address is different. 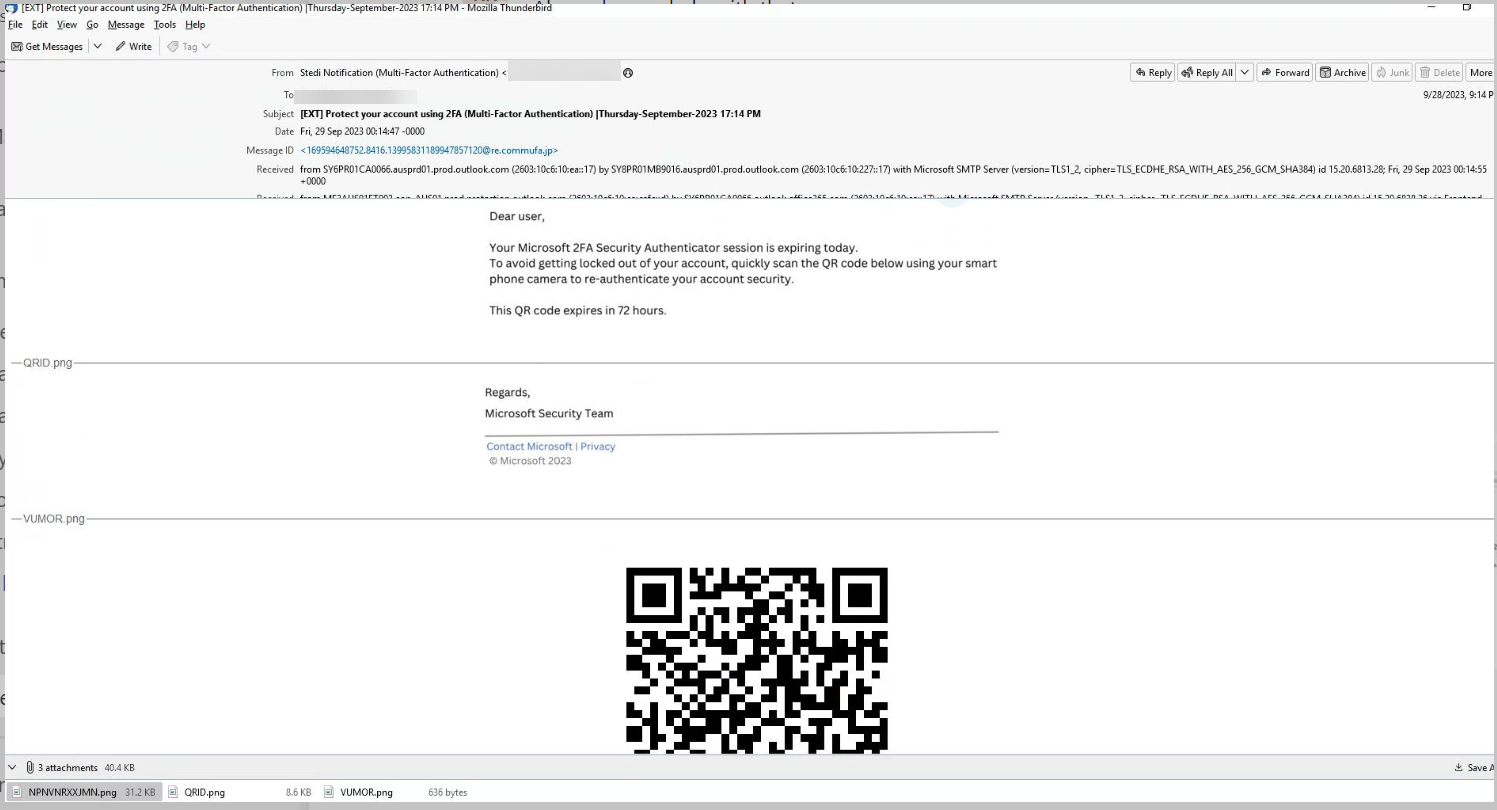
Once the user scans the QR code, they will be redirected to a page that looks like Microsoft but is in fact just a credential harvesting page.
Techniques
Hackers have been using scanned documents in order to hide text for a long time. The attack would work like this: There would be an image with the text and that would bypass some language analysis tools.
To combat that, you need Optical Character Recognition or OCR. OCR converts images to text to understand it.
Hackers then found another thing to get around it, which was a QR code.
In order to combat these attacks, it’s a little trickier. You need to add the OCR into a capability to detect QR codes, translate them to the URL that hides behind the code and run that through URL analysis tools.
For us, we’ve been protecting against QR codes for a number of years and actually deployed it within a few days. It’s an example of how we think philosophically. It’s all about having different tools in order to respond to changes in the attack landscape on a dime. We don’t always know what direction hackers will go in next. But we do have the foundational tools to combat it, from being inline to wrapping URLs, emulation tools, opening encryption and more.
When an attack vector gains steam, like QR code, we can look at our deep bench of tools and capabilities to build a solution in no time at all.
For QR codes, we use our QR code analyzer in our OCR engine. It identifies the code, retrieves the URL and then tests it against our other engines. In fact, the existence of a QR code in the email message body is an indicator of an attack. Once OCR converts the image to text, our NLP is then able to identify suspicious language and flag it as phishing.
Hackers will always try new tactics and techniques. Sometimes they’ll bring back old methods. Sometimes they’ll hijack legitimate things like QR codes. Whatever it is, having a full tool kit to respond is critical.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
- Implement email security that leverages OCR for all attacks, including Quishing
- Implement security that uses AI, ML and NLP to understand the intent of a message and when phishing language might be used
- Implement security that has more than one way to identify malicious attacks





