This attack report covers a massive attack on Office 365 users that leverages the trust Office 365 puts in its own links.
How it works
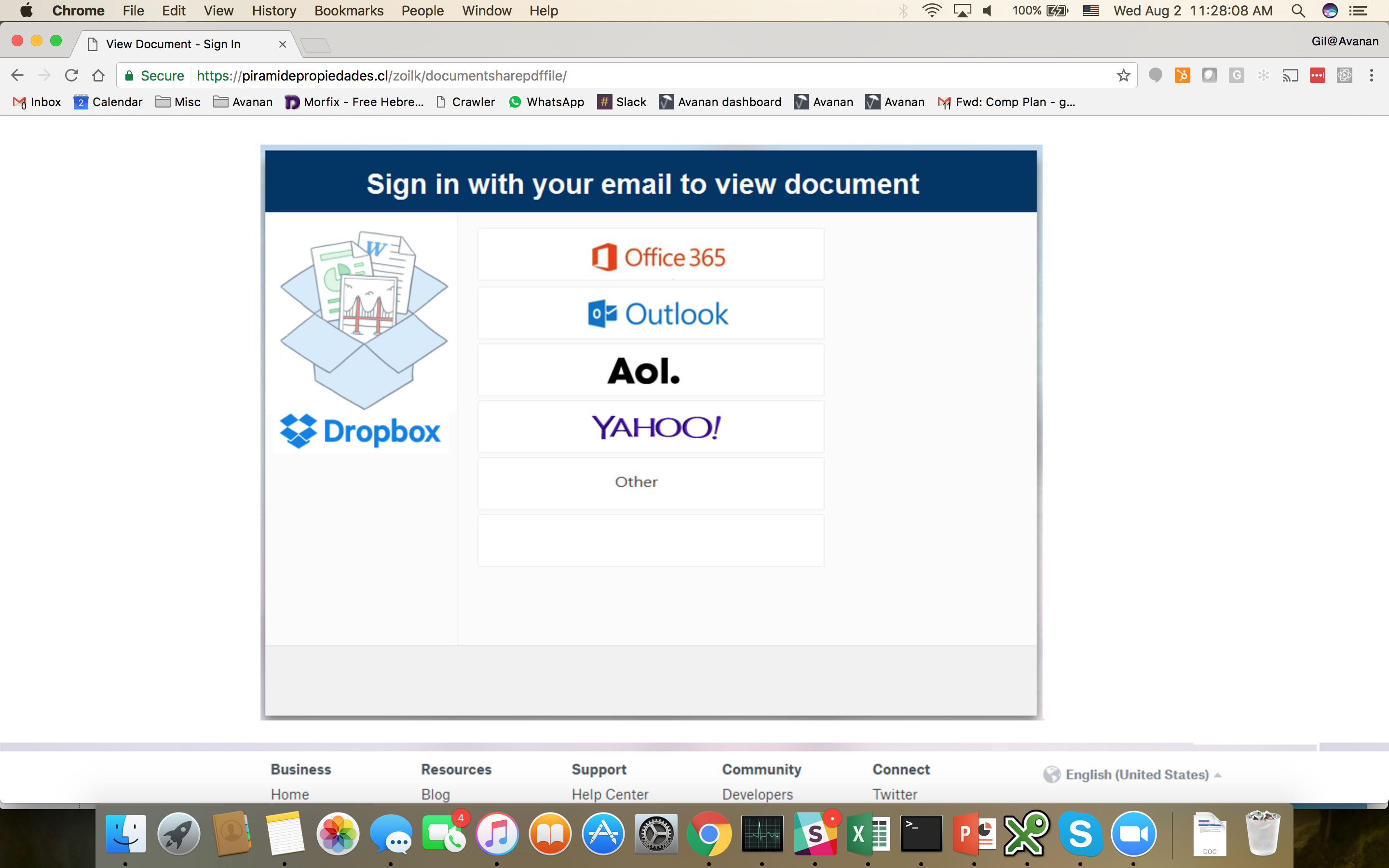
Most of the attacks come as an email with a genuine invoice from a commonly used online site, with a publicly open link to Office 365 Sharepoint. Once the user clicks the link, a javascript-based file starts to run and infects the endpoint.
Here's one example of one such email:

The link (INV-0015579) actually points to a malicious file hosted in Office 365 Sharepoint:
https://nexusbusinesstechnology-my.sharepoint.com/personal/malam_nexusbusiness_com_au/_layouts/15/guestaccess.aspx?docid=*******&authkey=******
How it is bypassing Office 365 security
Many of the phishing emails we have seen have links to external websites and through reputation testing and Block Listing, Microsoft's Office 365 default security is able to block them. But this is why this one is so challenging - it's a link to Sharepoint, which Office 365 trusts by default since it is its own application. Even if Microsoft's security team were able to block the specific file, the hackers would quickly create another link in Sharepoint and move to that one.
So, part of the core issue is that Microsoft does not extend its best security tools to native applications such as Sharefile and OneDrive. Most people would assume that files on Sharepoint and OneDrive would be scanned for malware, but the fact is that the scanning tools Microsoft uses for Office 365 are not used for files within Sharepoint and OneDrive files. Even if the malware is identified once, the same file in a different location in Sharepoint will not be blocked.
How do we know it is coming from China?
What is the identity of the attackers? This is obviously a speculation, but as Avanan's security team analyzed the attack, they tracked some information that links to Chinese hackers. For example, in the email shown above, the hackers have tried to impersonate xero.com, a popular account platform, but some of the other links point to a domain xeromc.net. Of course, hackers can fake this data, but aparently, this domain was registered yesterday from China. Here's the whois information behind this domain:

What Can You Do?
Avanan's anti-phishing machine learning algorithm detected this attack based on several factors. Factors like domain impersonation, together with sender email address, sender-receiver email history, and more allowed the Avanan anti-phishing machine learning to flag this as an attack and block it.
Avanan leverages over 200 indicators ('features' in the words of data analysts) from multiple vendors to conclude if an email is a phishing attack or otherwise malicious. This novel algorithm is deployed as an app within the Office 365 app store, and can be deployed in seconds, catching exactly the type of attack that Microsoft misses.
Contact us today and in 5 minutes and we will scan your company's inboxes at no cost for the phishing attacks that are there right now.