Hackers Attack a Vulnerability in Office 365 Handling of Punycode
Avanan’s cloud security researchers uncovered a new attack method against Office 365 business email that goes undetected by Microsoft’s Office 365 default security. The attack includes a phishing scheme to steal Office 365 credentials, and leverages a vulnerability in how Office 365 anti-phishing and URL-reputation security layers translate Punycode, a method for encoding domain names with Unicode characters.Puny-Phishing: Background
Punycode is a method added to the Domain Name System (DNS) in order to support non-ASCII characters within a web URL. For example, the Swiss bookstore bücher.ch would have an ASCII URL of xn--bcher-kva.ch which renders the non-ASCII umlaut ü.
The first punycode phishing attacks used non-ASCII characters to fool end-users into clicking URLs that looked legitimate, but substituted similarly-shaped letters from different alphabets to spoof the site. For example, the site http://www.xn--pypal-4ve.com/ looks like http://www.pаypal.com/ when rendered in the URL, but goes to a completely different site.
The New Puny-Phishing Attack
What makes this attack different is that instead of fooling the user, it fools the anti-phishing filters found in Office 365 and other email phishing protection systems. Hackers have identified a gap in the Office 365 phishing filters and are starting to leverage it to compromise accounts.The New Puny-Phishing: How it Works
To explain this attack, we will use an example from a real attack captured in early December 2016. The attacker sent a fake FedEx email with a benign looking URL that goes to a malicious site.

So far, this is very typical. The user sees “legitimate.com” but the underlying link goes to "malicious.com." These kind of attacks are easily detected by phishing tools that follow the underlying link to find the malicious site.
What makes this attack nefarious is that by using Punycode and a flaw in the phish-detection engine, the URL actually goes to two different sites: one followed by the malware protection filter, the other followed by the end-user’s browser when he or she clicks on it.
In this example, the email HTML code looks like this:
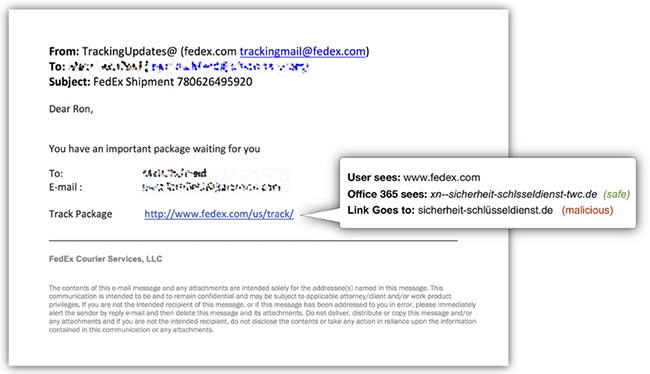
The root of this vulnerability is that Office 365 default security apparently treats this domain as plain ASCII when checking the legitimacy of the domain name. When testing the domain xn--sicherheit-schlsseldienst-twc.de as plain ASCII, it resolves to IP address: 81.169.145.66 (located in Berlin, Germany) that does not reveal any malicious intent. Therefore, the email is allowed through to the users’ inboxes.
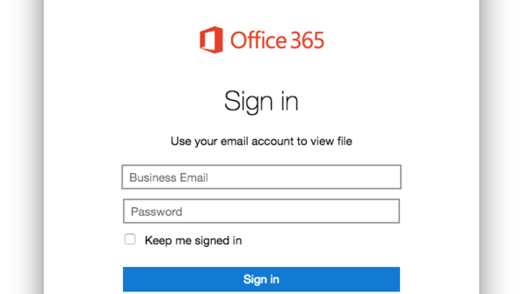
But when a user clicks on the link, the browser translates the address to its Unicode format: sicherheit-schlüsseldienst.de that points to a different IP address: 92.242.140.21 (located in Belfast, Northern Ireland), which presents to the victim with a fake Office 365 login page to obtain the user's Office 365 account ID and password.
 Attack Targets Office 365 Credentials
Attack Targets Office 365 Credentials
Analysis of the attack indicates that the hackers are particularly interested in Office 365 credentials.
- Almost all instances of this email have been found within corporations that use Office 365 for their corporate email and,
- the landing page for each of the malicious URLS is a fake Microsoft login which
- specifically asks for a “Business Email” account.
With the growth in Office 365 for corporate email, hackers are shifting their focus. The characteristics of this particular attack disclose the hacker’s intent to deceive Office 365 users into providing their login credentials.
What Can I do?
Contact Avanan, and we will provide you a free tool to scan your Office 365 inboxes to see if you were a victim of this attack. We can also recommend a list of security solutions from leading vendors on our cloud security platform in order to protect your users from this and other types of attacks.





