We’ve been writing recently about how hackers are utilizing legitimate services to send out phishing campaigns.
We’ve seen it used from Google, QuickBooks, PayPal and more.
There are a few reasons behind this trend. One, it’s simple. Hackers are able to create free accounts with these services and send them out to multiple targets. They then can embed a phishing link within a legitimate document and email it directly from the service. The email is legitimate—it comes directly from the service and will pass all SPF checks and other standard things that security services look for.
Hackers have a ton of tools at their disposal to conduct these attacks. A new favorite is Microsoft’s file-sharing service, SharePoint.
In this attack brief, Check Point Harmony Email researchers will discuss how hackers are using SharePoint to send out phishing links.
Attack
In this attack, hackers are using SharePoint to send phishing links.
- Vector: Email
- Type: BEC 3.0
- Techniques: Social Engineering, Credential Harvesting
- Target: Any end-user
Email Example
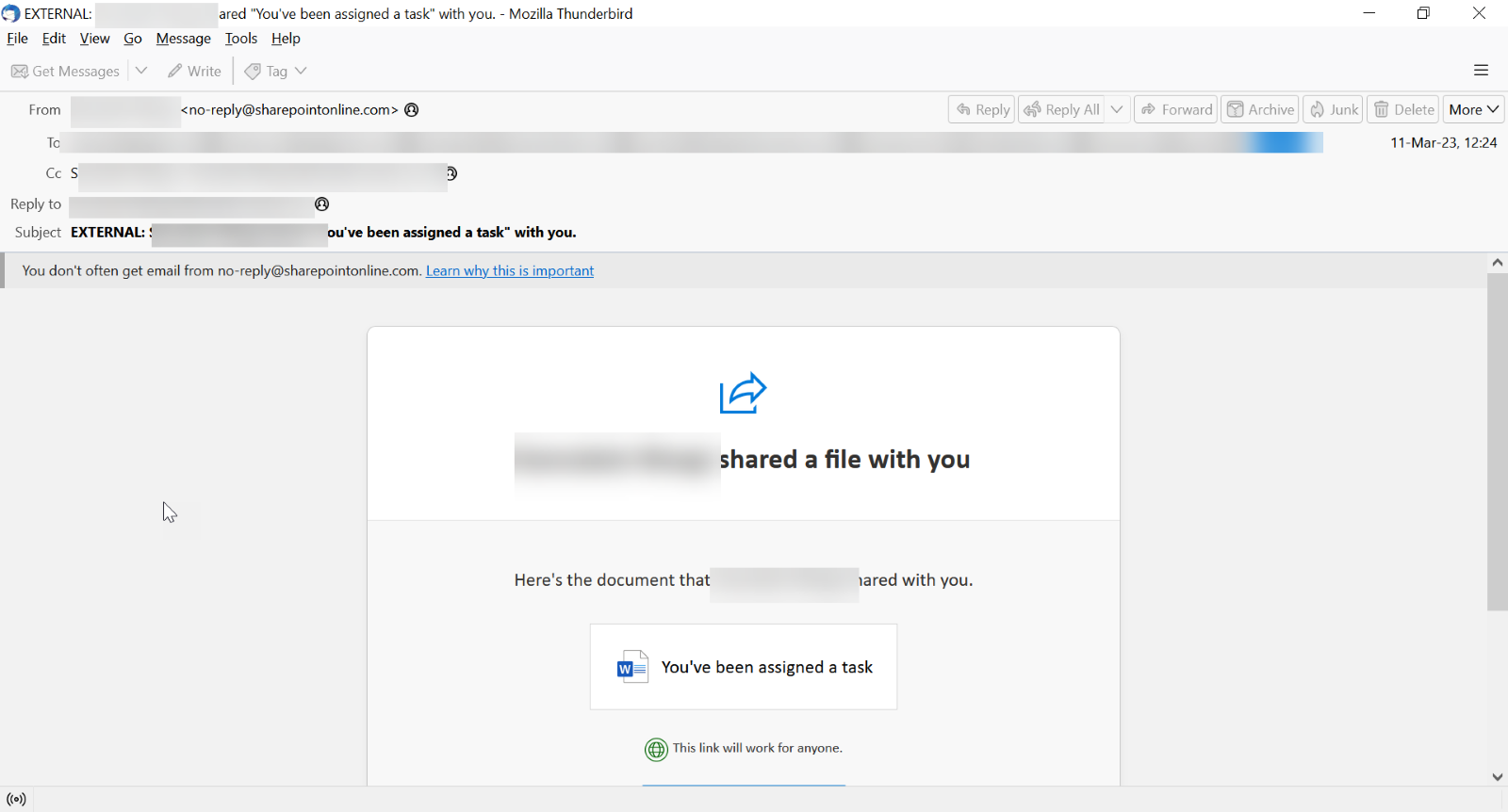
This attack starts with the recipient getting a notice from SharePoint that a file has been shared.
When clicking on the link, you are redirected to a legitimate SharePoint page.
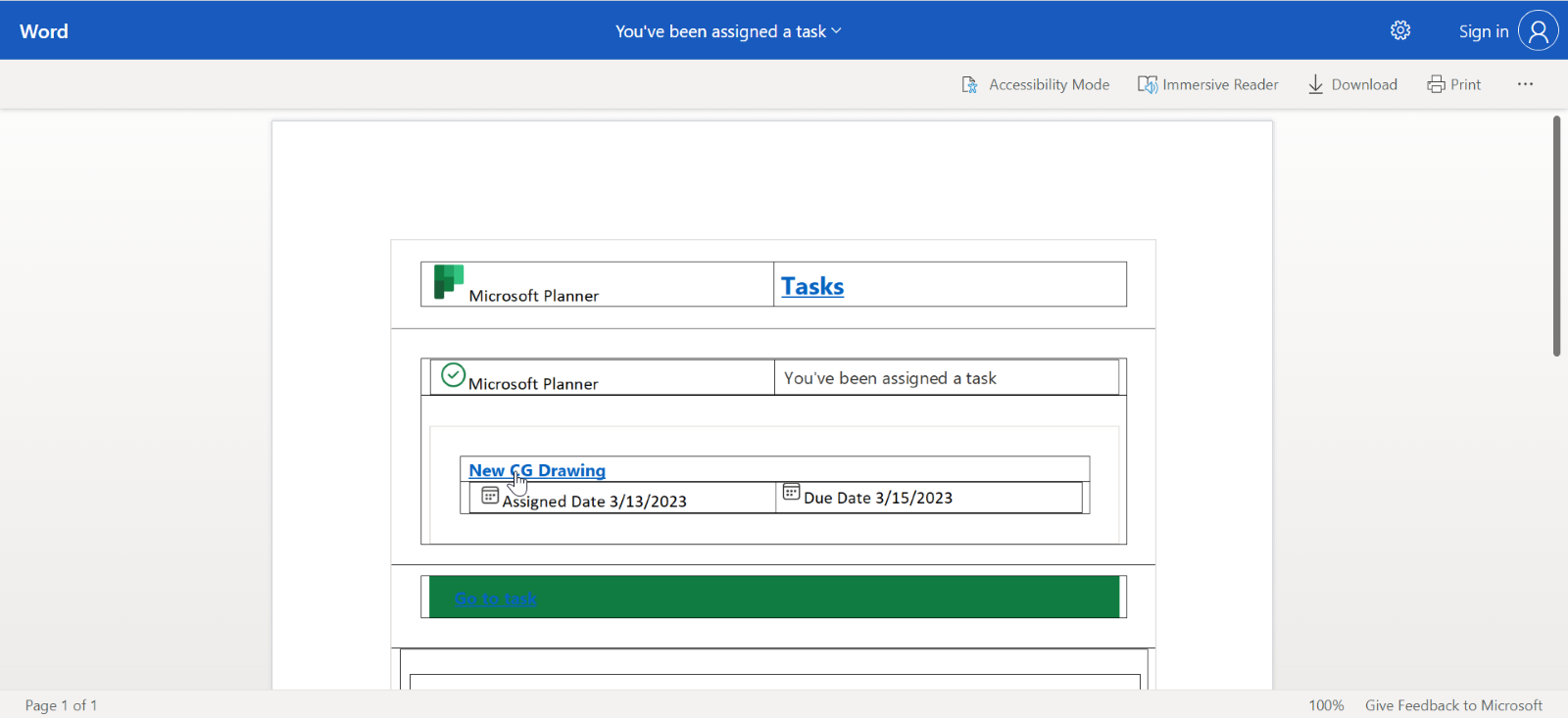
What's tough here is what’s linked. The “New CG Drawing” does not go to another Microsoft page. Rather, it goes to a phishing site that has since been taken down. All the other links are legitimate.
Techniques
Utilizing legitimate services to send attacks is the latest trend of 2023. We call it BEC 3.0, and it’s the next evolution of Business Email Compromise. No need for intense social engineering, no need for drawn-out back and forth.
These are incredibly easy to execute and just as hard to stop. There are almost no malicious indicators. It’s a legitimate service, sent at a legitime time, from a legitimate source, with legitimate language. It’s hard to tell if it’s fake or not, let alone malicious or not.
So what do you do? You have to stop at the perimeter of the attack. Link protection is huge—emulating pages behind links to see the true intent. So even if the user clicks on the malicious link in SharePoint, you can still analyze it. Analyzing sites for zero-day phishing indicators is huge, too, as is utilizing OCR to find fake icons and logos.
This attack form is not going anywhere. If anything, it will continue to gain in steam. To combat this, a new approach is needed.
Check Point researchers informed Microsoft of this campaign on July 25th.
Best Practices: Guidance and Recommendations
To guard against these attacks, security professionals can do the following:
- Implement security that uses AI to look at multiple indicators of phishing
- Implement full-suite security that can also scan documents and file
- Implement robust URL protection that scans and emulates webpages
H






