As happens with all major news events, Avanan is tracking a tremendous number of fake sites, emails and even phone calls and texts which all offer an insider's access to the COVID vaccine.
Using Business Email Compromise techniques, hackers create thorough, realistic copies of the websites they spoof and can do so in a matter of days. Based on the pattern and sophistication of the attacks , these are incredibly organized and targeted to larger organizations.
As more vaccines get approved, Avanan analysts expect to see similar attacks propagate at scale.
The Attack: Avanan researchers are seeing a massive rise in sophisticated vaccine-related BEC email related to the COVID vaccine. For example, this email purportedly comes from the head of vaccine distribution of BioNTech, one of the Pfizer partners that have just received emergency FDA approval.
.png?width=550&name=BionTechEmail%20(1).png)
Though Avanan stopped this attack, it passed by the scanners of Microsoft ATP and Proofpoint.
This attack is effective for a number of reasons. There are no links to the site in the email, which allowed it to bypass many traditional phishing filters.
The email itself is well-written, with no easily discoverable spelling or grammar errors.
If the user was to Google the domain, they would be directed to a fully functional website that includes contact information matching what's in the email.
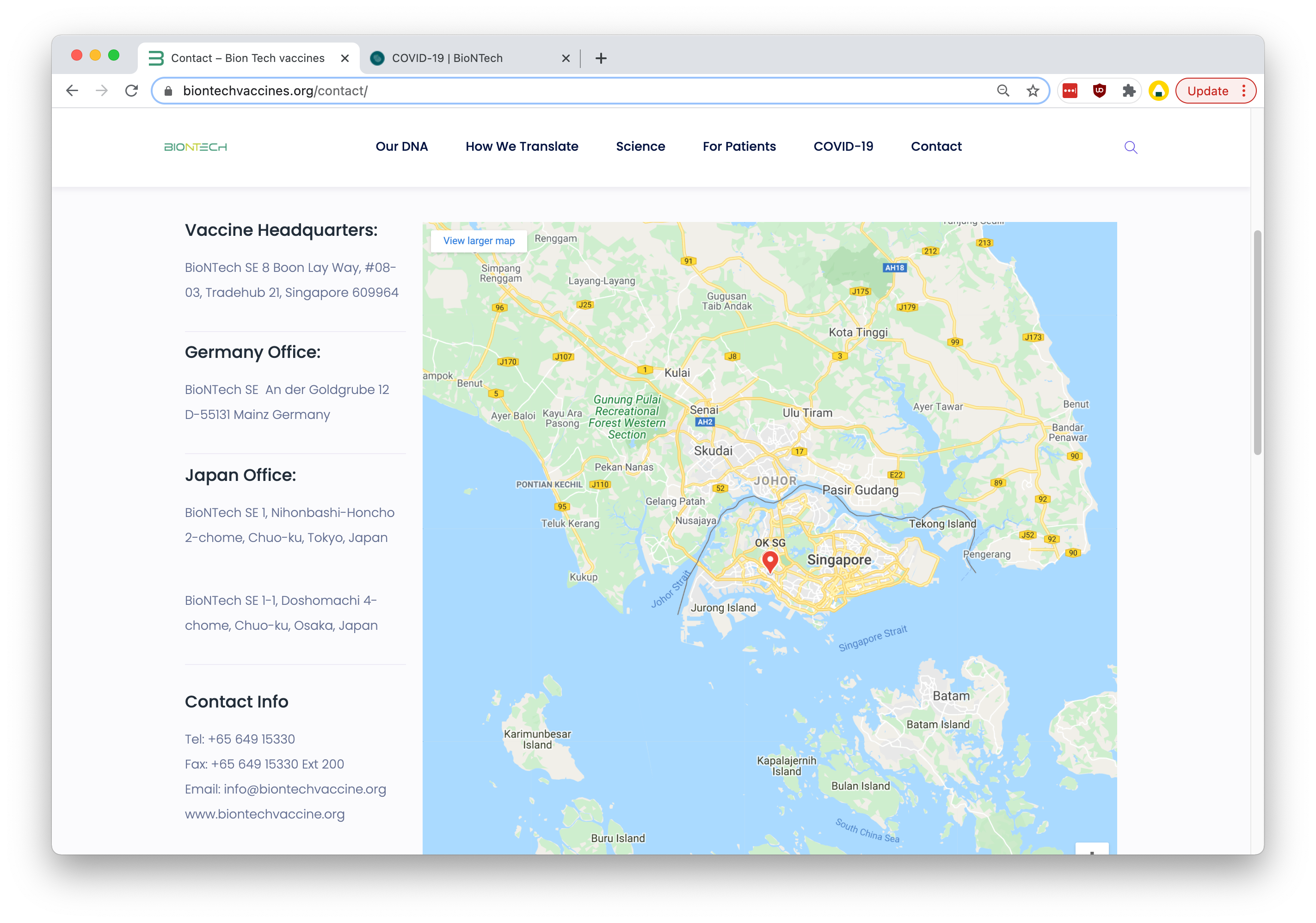
The only difference in the contact page is there's a "new" vaccine headquarters in Singapore. It has a working email address and a disconnected phone number.
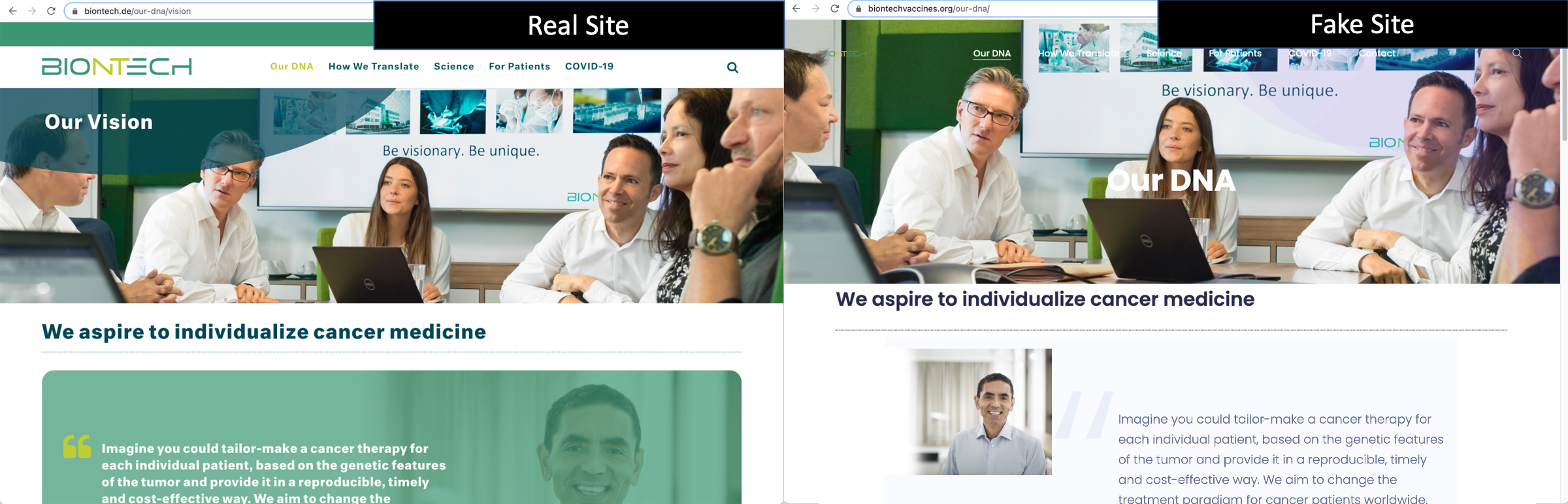
If the user were to explore the website further, they would find a close facsimile to the BioNTech website.
Another reason the attack is effective is the timeline.
Pfizer-BioNTech announced an effective vaccine candidate on November 9th. The attackers registered the domain "biontechvaccines.org" on November 11th and within days, had duplicated the entire BioNTech website with a WordPress version on the fake domain. On December 11th, the Food and Drug Administration approved the BioNTech vaccine for emergency use.
A few days later, the first spoof email utilizing BioNTech went out to end-users.
Biontechvaccines.org (active as of this writing) is not the BioNTech website, but looks very similar.







