In 2016, the infamous Mirai botnet briefly derailed the internet, shutting down Dyn servers responsible for internet traffic and much of the internet’s infrastructure. Despite the scope and consequences of the global attack, botnets remain on the periphery of general security awareness. Even so, Botnets swamped the 2018 Verizon Data Breach Report by order of magnitude: “attacks on web application authentication mechanisms driven by banking Trojan botnets happen—a lot. Had we included the almost 40,000 of them as part of the analysis, nothing else would come to light.”
What are botnets?
Botnets, a portmanteau of robot networks, describes a system interconnected computers that can be used to perform various tasks, typically for nefarious reasons. Users catch botnets like a cold. Much like the invisible spreading of germs, botnets infect computers and IoT devices—smartwatches, smart refrigerators, PlayStations, even Teslas—through malware Trojans designed to install the malicious code that allows the hacker to spawn and control their bot regime. This code is often shared through peer-to-peer services like Google Drive or SharePoint, but can take the form of adware, files on torrent sites like Putlocker, and pornography clips.
From there, the bad actor enlists the device in a somewhat anonymous army designed to co-opt devices and deluge firewalls, networks, load balancers, DNS servers, and applications. Botnets have evolved to the point that the bot herder can use any bot to control the botnet, so they no longer has to risk using their personal device as a command and control server to coordinate the attacks, which can be readily traced by law enforcement. The dispersion and mass of the chaos botnets wreak on the internet is precisely what makes them so successful.
Why do botnets matter?
Disruptive botnets can shut down entire websites and, potentially, the internet itself. They’re difficult to secure against because they exploit browser security vulnerabilities, forgotten plugins, operating systems, outdated hardware/software, and unwitting users. Conceptually, they challenge widely held ideas about ownership of and responsibility over devices. If an unsuspecting user is compromised and their device contributes to a large-scale click fraud campaign, then are they, too, responsible for this and the other cyber crimes that bot herders execute?
This network of infected devices can be thought of as the composite of other attack types, such as ransomware, malware, phishing, and keylogging, to name a few. As such, botnets have many uses. In simpler cases, botnets can hijack email to disseminate spam. They can be used to generate fake internet traffic on a third-party website for financial gain. On the darknet, botnet masters can sell or rent their zombie army to other hackers to control at their discretion—typically to spread ransomware, perform cyber attacks, or harvest personally identifiable information. They can also be used to mine cryptocurrency. Botnets can even skew election polls. They are most commonly known for DDoS attacks, though.
Common botnet attacks and how to prevent them
The profitability and multi-vectored nature of botnet attacks make them a hacker favorite. For even the savviest users, botnets are difficult to detect. A frequently unresponsive browser or spike in error reports may be a sign of botnet compromise, but not necessarily—especially for many IoT devices, where the user interface is less interactive.Therefore, a preemptive defense strategy against botnets is the most effective option for how to prevent attacks
Email Spamming
Hackers use email to spread malware like a plague. The unsolicited attachments or links that often come with these emails are basically invitations to join a botnet. Credential harvesting trojans, such as spoofed login pages for Google Drive, PayPal, or Netflix, are the driving force behind the continued success of this method. Once the account has been compromised, worms and drive-by downloads can also be spread from that account.
Botnet Defense
Add multi-factor authentication to your email, then guard it even further with an authenticator app. This basic and automated protection shields you from the mass identity theft botnets are often designed for. Avanan's email security scans and sandboxes all incoming files to detect malware, effectively blocking the initial entry point for botnet hackers.
Keylogging
Botnets can install keylogging programs onto your device. Still, recording every keystroke on thousands of devices would render that pursuit meaningless. That's why hackers filter their keylogging malware to detect words like "PayPal" or "login." From there, hackers can instantly capture credentials that open the floodgates to a wealth of valuable PII. It is exceedingly likely that a user would have the same credentials for PayPal as they would for their Bank of America app.
Botnet Defense
Installing a password manager like LastPass that encrypts, stores, and generates passwords for you guarantees that keylogging scripts will not surface valuable credentials. As a result, hackers will never see your credentials because you never have to type passwords into your keyboard.
Installing Advertisement Add-Ons
Botnets capitalize on human error and angst. A host of plugins float around the internet, waiting for users to integrate them into their browser. Frequently, these plugins claim to be helpful products like malware scanning tools, offering to prevent the very kind of attacks they execute. They might also take the form of services unrelated to device security, such as the oddly bland advertisement shown below.
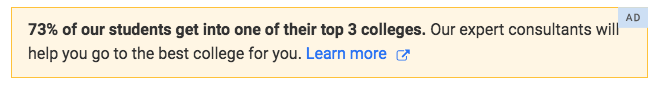
Botnet Defense
Prevention for this breed of attack is simple: perform a Google search for the product being advertised in the ad banner to confirm its existence and validity. To add another layer of defense, consider switching to a browser like Duck Duck Go, which is specifically designed to cloak you from the prying eyes of advertisers. After downloading the extension, you will no longer see the relentlessly annoying ads that flood your favorite sites.
Click Fraud
Researchers at University of Twente in the Netherlands found that "the most profitable undertaking is click fraud, which generates well over $20 million a month of profit." Bot herders frequently create fake websites on which to host advertisements for third-parties for profit. For every click on an advertisement executed by a bot in a botnet, botmasters accrue a percentage of advertising fees since the advertiser rewards the publisher for engagement with their content.
Botnet Defense
Securing your Wifi with a strong VPN creates an encryption tunnel that is almost impossible for hackers to penetrate. It’s no secret that choosing the best VPN service is difficult. When choosing a VPN, it is important to stop and think a little about the reasons why you need a VPN in the first place. One that unblocks streaming sites might not be sufficient for a tech-savvy user with exotic needs. The list from Cybernews, sums it all up nicely.
How to identify if your device is part of a botnet
Consult the following sites to quickly determine if your IP address is part of a botnet:
How to remove yourself from a botnet
If you have found that your IP address has been used in a botnet attack, here are some methods to restore the privacy and integrity of your devices.- Reset your router.
- Switch to alternative DNS providers, like OpenDNS.
- Download anti-virus software.
- Remove factory-installed passwords on IoT devices and routers and replace them with long, strong passwords that use a balance of numbers, letters, and special characters.
- Upgrade your router, even if it is working fine. New routers have more robust security protocols.
Conclusion
Despite the immense power that botmasters wield over their zombies and the internet itself, botnets rely on common hacking methods to gain footing. Most botnet attacks can be avoided using basic security practices.
For general defense against botnets, invest in a firewalling router and don't click on pop-up ads, suspicious email attachments, or unsolicited software downloads. Organizations that are serious about security should use more advanced cloud security tools, such as Avanan's cloud security platform, to prevent botnet attacks.