A rapidly increasing attack campaign is hitting inboxes.
Since the beginning of April, Avanan researchers have uncovered an attack reaching over 1,000 inboxes across multiple organizations and sectors. The attack relies on obfuscation to fool Natural Language Processing to reach inboxes. These attacks were missed by ATP, but stopped by Avanan.
The attack works like this. The email is rendered one way in the email client, presenting it as a SharePoint document; but hackers are using Base64 and UTF-8 to encode the "From" and "Subject" lines, ensuring it gets past Natural Language Processing scanners.
Here's what the email looks like in a typical mail client: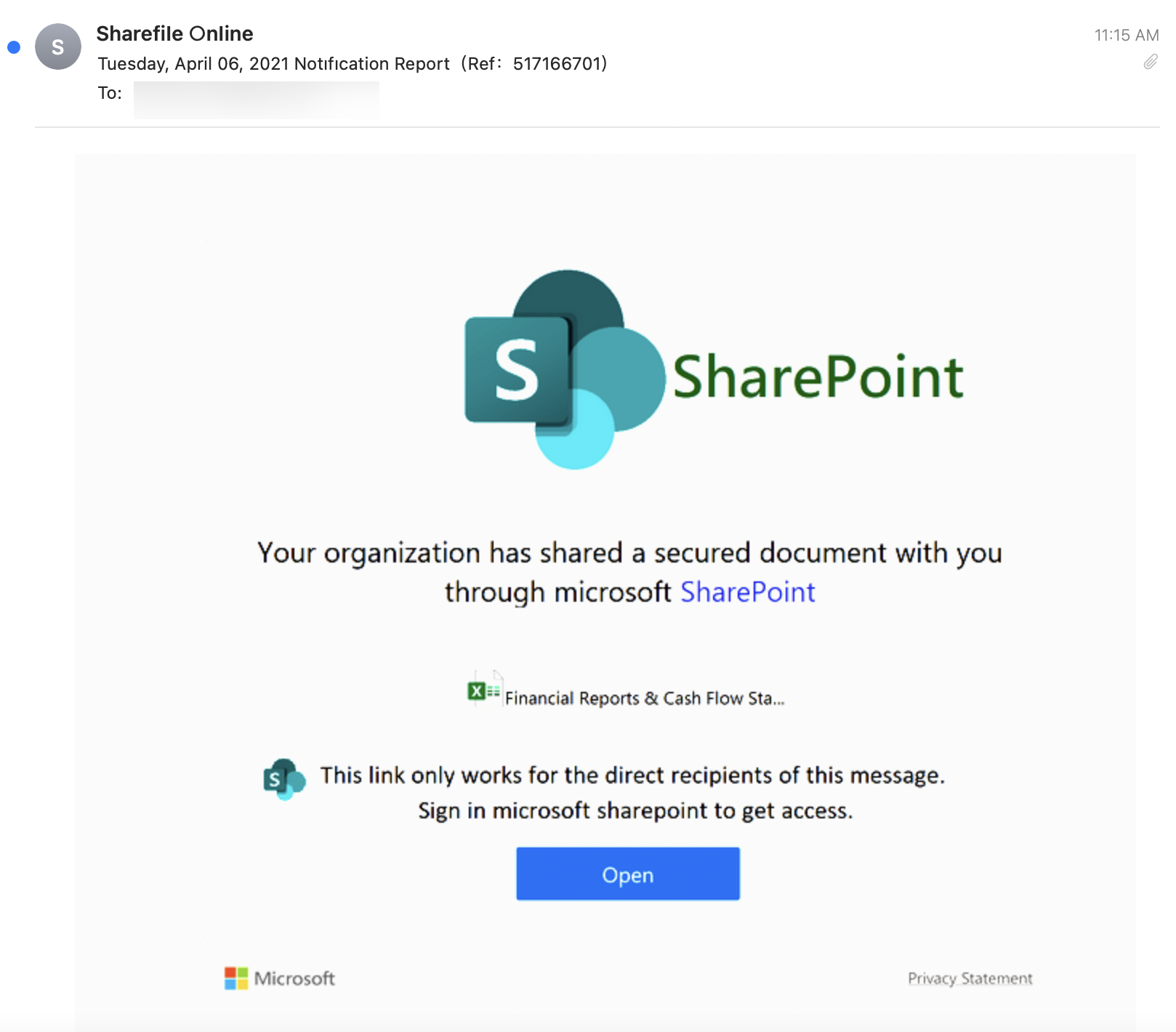
This looks like a fairly standard email, though there are plenty of grammatical errors throughout and there are mentions of two competing products, SharePoint and ShareFile. That's not the point—what matters, of course, is getting end-users to click on the "Open" link and steal some credentials.
Upon inspection, however, you'll notice how the hackers got into the inbox: they obfuscated the "From" and "Subject" fields:
-png.png)
When other NLPs see this random string of characters, nothing looks malicious. Avanan detects such non-ASCII characters and uses them as one of its Indicators of Attacks (IoAs).







