Looking at API/AI Enabled Email Security Vendors?
You’ve made the decision to explore the next generation of email security and are looking at several different vendors. Perhaps you’ve taken a demo and are impressed with the stories they tell. These include claims like, “They’ve never lost in a POC/trial” (FYI this we can tell you with 100% certainty is false). Some come with the sales and marketing glitz of Silicon Valley trying to convince why their AL/ML built for social media somehow translates to better AI for cyber security.
If you can't tell much difference between them, there is a simple question you can ask to cut through the smoke and mirrors:
“Do you prevent inbox incursions?”
An inbox incursion is when phishing emails are available to the end user for any length of time. In such cases, the vendor remediates them post-delivery. This means the email is available for the end-user to open up and click on the link. They may try to convince you that it's "only for a second or so" or that users will "barely notice". Let's be clear, any email phishing email available to the end user for ANY length of time (5 seconds, 20 seconds, 183 seconds), is not the best that is available. Our research shows the average length of time is 183 seconds.
After they are done with their explanation, make sure to clarify by asking point blank:
“Can you prevent phishing emails from being delivered to the end user's inbox?”
Prevent is the key word! And if they don’t have a reasonable explanation as to how they prevent inbox incursions, perhaps what they are really about is email response and not email security.
The Case for Prevention over Response:
Better Security & Time Savings
"Letting the email into the inbox for any period of time is not ideal and not the best form of email security"
It should go without saying that any “email security” solution that doesn’t prevent inbox incursions isn’t really providing email security. A better name for these solutions might be email response solutions. It’s akin to buying a Rolex from a guy on the street in a trench coat. Not the real thing.
Letting the email into the inbox for any period of time is not ideal and not the best form of email security. It gives users the ability to make mistakes and in the game of email security, the goal should be to avoid the chances for mistakes.
Prevention is our philosophy and it's 101 when it comes to real email security.
Better Time Savings
Better security starts with prevention. But better security isn't the entire story. Prevention will not only make you more secure, but it will save you more time.
In a study we conducted last year, 23% of the SOC Team’s time is spent managing the email threat. This includes reviewing end-user reports of suspicious emails to the SOC or security team. In one case, 70% of the daily support cases were related to email security issues. With each end user report taking on average 7 minutes to investigate, it’s easy to understand how these alerts can collectively take up considerable resources. No wonder we are experiencing the burnout of the SOC.
"23% of the SOC Team's time is spent managing the email threat"
When it comes to which solution will save you more time, compare the workflows side by side. On the left, you have Avanan customers in our patented protect mode where malicious emails don't reach the inbox. On the right you have what the other API vendors offer, which is email response.
|
Avanan in Protect Mode |
Email Response Vendors |
|
|
The bottom line: solutions that don't prevent inbox incursions aren't the best form of email security when it comes to saving your SOC and security teams time.
Better AI/ML Requires Better Data
"The best email security requires the best threat intelligence"
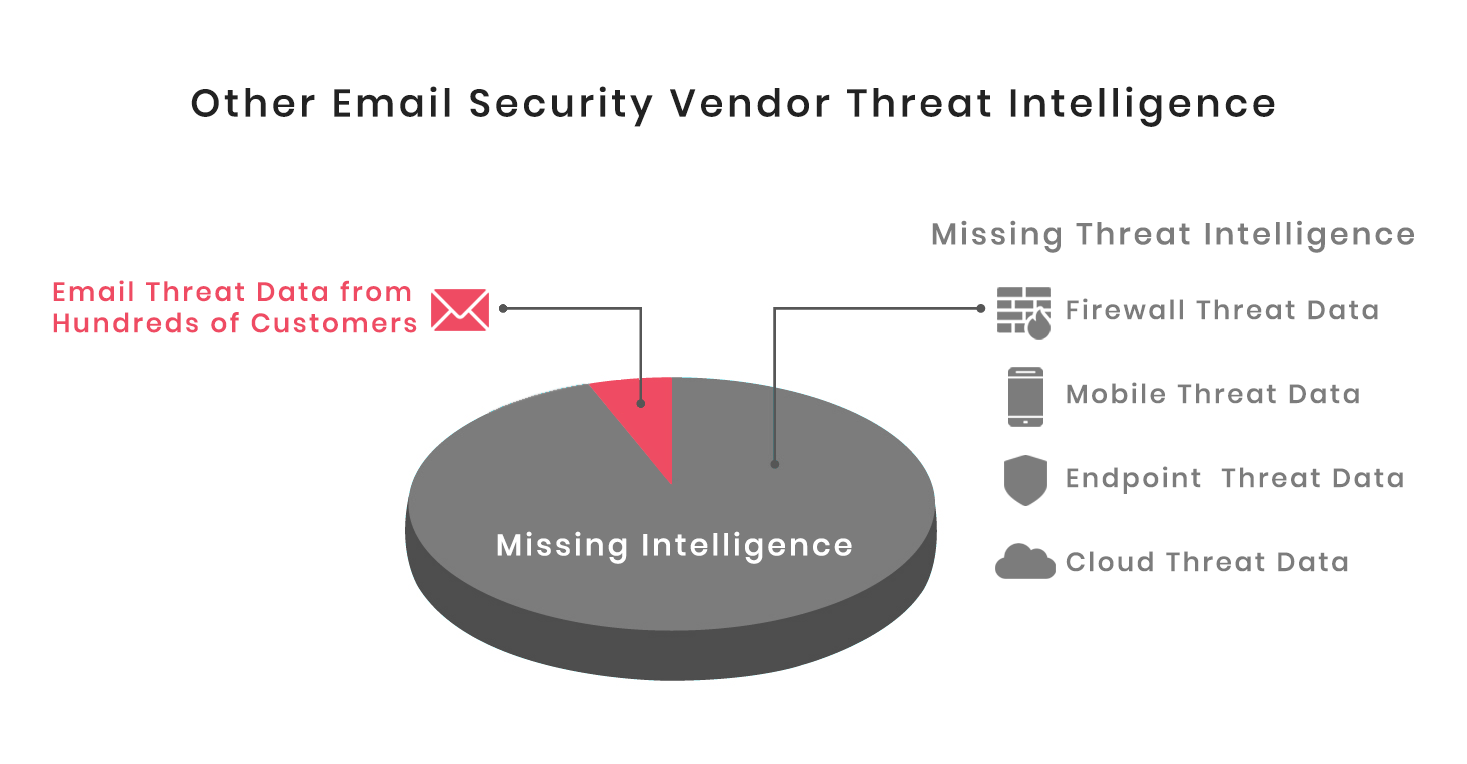
The threat intelligence for which the AI/ML is trained is the single most important factor in determining the effectiveness of the AI/ML algorithm. The richer the intelligence, the better the catch rate. For the "stand alone" email security vendors, their intelligence is limited. It's limited in terms of the types and magnitude of their threat feeds. In general, they are only looking email threat intelligence with a small sample size (only hundreds of customers). This is myopic.
Avanan's AI is powered by the world's most extensive cyber threat intelligence database and extends well beyond email threat data to include threat data from millions of devices including mobile, network, endpoint, and cloud
Compare the difference in threat intelligence datasets below:
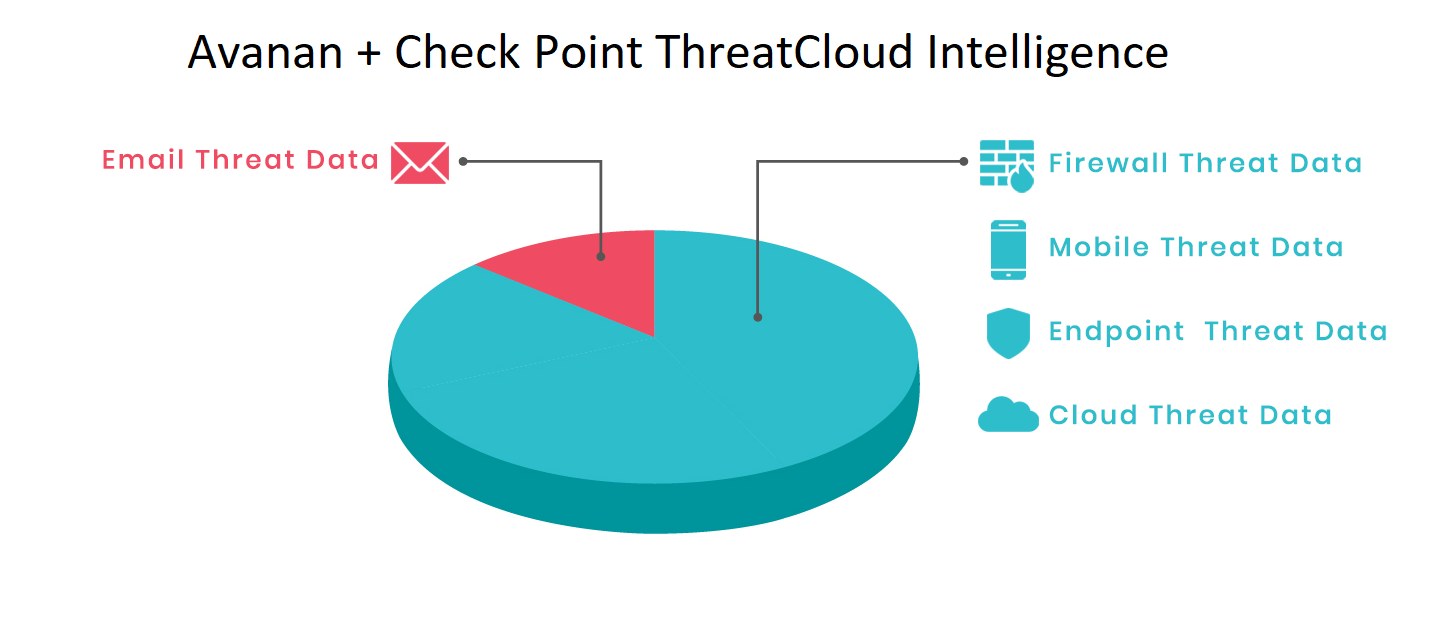
To put the magnitude of Check Point's ThreatCloud intelligence into perspective:
- 150,000 connected networks - Number of connected networks reporting into Check Point's ThreatCloud with millions of endpoints worldwide
- 12 Device Types - Number of device types reporting into ThreatCloud including endpoint, mobile, network device, cloud, and email
- 86 billion - Number of transactions processed by ThreatCloud per day
- 7,000 detections of zero day threats detected each day
- 650K suspicious websites detected per day
- 6.8 Billion malicious website connections blocked last year
- 185 Million malware downloads blocked last year
- 778 Million vulnerability exploit attempts last year
- 200+ of the world’s renowned threat research team - full time threat researchers discovering some of the most significant unknown software vulnerabilities
- 30+ AI Technologies under one single product
"Avanan's AI is powered by the world's most extensive cyber threat intelligence database and extends well beyond email threat data to include threat data from millions of devices including mobile, network, endpoint, and cloud"
Avanan: You Deserve Better Email Security
The best email security starts with a solution that prevents and doesn’t just respond. It has to incorporate AI/ML that is trained on a comprehensive threat intelligence that extends beyond the email data of a few hundred customers.
Get the Facts
For a detailed breakdown of how Avanan compares to the email security responders, click below:







