Introduction
Email security is a competitive marketplace. There are a number of competing solutions that all do somewhat similar things. That means when it comes to competitive bake-offs, the customer is faced with a tough choice.
It makes things even tougher when competitors decide to sling mud. In this blog, we’ll showcase what [Desperate API Vendor] is saying to prospective customers and their last-ditch attempt to make their case. We redacted the name of the competitor.
Before we get to that, we want to bring back to light our key strengths and highlight what makes Check Point the best email security solution in the market today.
Why Check Point is the Best for Email Security
- Check Point Email Security offers the Greatest Capabilities with the best AI
- Check Point is a Real Cyber Security Leader
- Check Point has the most experience servicing enterprise accounts
1. Greatest Capabilities with the best AI
More capabilities to make you more secure and save you more time
|
Pre Inbox Scanning with Post Delivery Remediation |
We do this because the best email security prevents malicious emails from ever hitting the end user’s inbox. Unique to Avanan. Also does post delivery remediation |
|
Mail Explorer |
Search and Destroy to search through thousands of emails using dozens of search criteria in seconds. Quarantine results in a click of a button |
|
DLP |
Allows customer to identify and prevent the sharing of sensitive content in all collaboration applications |
|
Advanced Sandboxing |
Check Point Sandblast represents the best zero-day sandboxing solution in the market today powered by Check Point ThreatCloud. |
|
Encryption |
Ensure sensitive information is protected and can be sent securely, meeting compliance needs for all customers |
|
All lines of collaboration |
Email, OneDrive, SharePoint, Teams, Slack - One solution; all lines of collaboration |
|
The best AI |
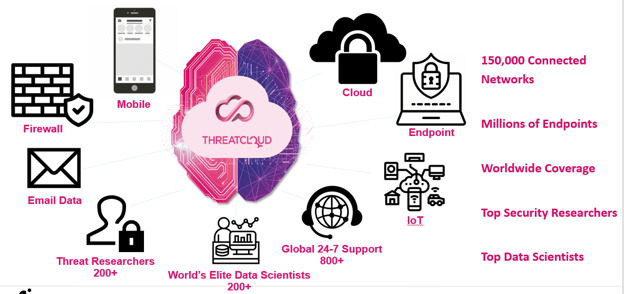
The best AI as a result of the best threat dataset from Check Point ThreatCloud |
2. Check Point is a Real Cyber Security Leader
A better AI comes from better data. Better data looks at much more than email data.
3. Check Point has the most experience servicing enterprise accounts
Myth vs. Truth
The following sections outline some of the myths being spread by our competitors in the email security space. We’re happy to always demonstrate through transparency why we are better.
Myth 1: The Check Point solution stops email delivery when there’s an outage
Myth: “With Avanan’s email rerouting, an Avanan or AWS outage stops delivery of all your email. There are multiple websites that report specifically on Avanan outages since they happen fairly often”
Truth: First, we fail open and fall back into “Detect and Remediate” mode which is the only mode you get with [Desperate API Vendor Name]. So when there is an outage, your email doesn’t get “stopped” from being delivered. Second, a “service disruption” rarely results in the outage that they describe. When we have a service disruption, which is rare, that impacts any aspect of our platform, we’re transparent and report on it. A disruption in a feature like our Mail Explorer has zero impact on deliverability. Their description is akin to saying a car won’t drive with a broken radio.
Myth 2: Desperate API Vendor has Magic that Prevents Email-Based Attacks in “Milliseconds” using 100% on APIs
Myth: “[Desperate API Vendor Name] purely relies on the API - no transport rules. And with the Checkpoint acquisition, Avanan’s Roadmap will be nowhere close to [Desperate API Vendor Name]”
Truth: Let’s take this into a few parts:
- Being 100% API is NOT a good thing as they are trying to spin it. In fact, this is a major problem for security minds that believe it’s best to not let emails reach the end user’s inbox or dwell for up to 30 minutes (See quote below from a customer that evaluated both us and the Desperate API Vendor in question). Vendors that rely 100% on APIs cannot provide an SLA on dwell time. Two reasons: latency and throttling by Microsoft and Google. Throttling is such a well-known issue that MS documents it here, here, here and here. Because of throttling, Microsoft specifically tells API vendors to be able to handle the infamous 429 error which is the error thrown when Microsoft starts to throttle:
- One way to avoid the 429 error is to reduce the number of API calls. Each time an email is delivered, it requires a series of API calls because the API vendor must retrieve a copy of the email. At least one API call to learn about the new message, another to retrieve the contents of the email. This doesn’t take into consideration API calls required for “remediation” post delivery. There is latency involved in each API call which of course increases dwell time on top of throttling issues.
- With regard to the roadmap, we’ll let our customers and prospects be the judge of who is better. But the fact is there is not another email security company that provides such a level of commitment to research and development and keeping our customers safe. Check Point spends $350M a year on R&D. Our threat research team is 150 strong with researchers from the world’s most elite cybersecurity organizations on the planet including IDFs Unit 8200. The research team of some of our competitors is generally in the low single digits. Further, our AI is powered by the largest and most complete threat dataset on the planet transacting 86 billion transactions per day…
- Our “Data Center” is not in Israel. We are hosted in AWS and we let the customer choose which country their data resides in. We have residency in numerous global regions and continue to add more each month
- There are a few reasons we retain some emails for a limited duration.
- Because we are a full-featured email security vendor, we offer up archiving as a service
- One of our most popular features is our “Search and Destroy” or “Mail Explorer” feature. This gives our customers the ability to search through hundreds of thousands of emails using any number of criteria within seconds.
- Standard data retention for Avanan:
- Clean or Pending messages: 14 days
- Quarantined messages: 180 days
- Metadata for all messages: 180 days
- The comment, “pulls your data out of your tenant” is technical sleight of hand. Do not be deceived. For any email security solution to work, it requires seeing the contents of the email and the attachment. In other words a copy of your email. There is no effective “remote scanning” going on that doesn’t require a copy of the email. In order for any vendor to know if the email is malicious, they MUST look at the contents of the email and attachments. If they lead you to believe there is some magic that doesn’t require a copy of the email, ask them to explain this to you. How will they be able to utilize AI/ML on the message? How will they be able to tell if there is malware embedded in the attached files?
“use the HTTP error code 429 to detect throttling. The failed response includes the Retry-After response header.”
Myth 3: Data Residency is in Israel for 30 days
Myth: “Avanan pulls your data out of your tenant and stores at their DC in Israel for 30 days. [Desperate API Vendor] only stores metadata of malicious emails”
Truth: Need to dissect this multifaceted myth into three parts
Myth 4: There is no downside with a 100% API-based approach
Myth: “They [Avanan] are not true API-based, bi-directional solutions. They use inline transport rules which is not the most effective way to combat BEC. [Desperate API Vendor] is a true bi-directional API that is not inline.”
Truth: Not sure what defines a “True API-based, bi-directional solution”. Also unsure as to how these buzzwords impact effectiveness, ease of use, or capabilities. The bottom line is that our approach yields better security and more capabilities. We’d be happy to go into as much detail as necessary to justify this or let our customers see every aspect of the product for themselves.
To the point about the “most effective way to combat BEC”... It’s a matter of choice. Is the customer OK with a 30 minute dwell time for malicious emails? Is being subject to throttling and latency to deliver security OK?
Myth 5: [Desperate API Vendor] prevents malicious email delivery in milliseconds
Myth: “With the competitors, malicious emails hit the end-user inbox prior to action/removal unless a customer alters their mailflow. With [Desperate API Vendor] there is zero change to mailflow.”
Truth: This is a stunning contradiction. Solutions either scan emails pre or post delivery. Pre delivery scanning (which we offer) will prevent delivery until the email is scanned and determined clean. Post delivery (which we also offer) removes the email after delivery. If this [Desperate API Vendor] is claiming they have magic that scans the email before delivery without taking a detour before the inbox, then it’s probably time for them to prove it and explain how. The question really is whether The Desperate API Vendor can prevent malicious email delivery. Is their dwell time really “milliseconds”? In reality no and we have laid out why using only APIs is technically impossible. But you don’t need to take our word for it. Have the Desperate API Vendor prove this in their trial. Put it to the test as the customer below did a couple of months ago to only see a 15-30 minute dwell time.
Myth 6: Desperate API Vendor Doesn’t use 3rd Party Solutions and Avanan Does
Myth: “They use 3rd party threat intel to supplement detection which impacts efficacy. [Desperate API Vendor] relies only on its own AI/ML, NLP, VendorBase, PeopleBase, TenantBase, AppBase to deliver the highest efficacy and lowest FP/FN rate in the industry.”
Truth: Avanan’s Sandboxing is Check Point Sandblast. Our AI is ours. Check Point’s ThreatCloud is ours. What we find interesting is the fact that this Desperate API Vendor can’t do malware sandboxing on its own. They leverage a 3rd party called Any.run. This point is conveniently missed from their stones. There is no match for any.run vs. Check Point’s Sandblast, especially from an unknown 3rd party vendor (see below “Daily Attacks Detected - How the malware sandboxing solutions compare”). Further, if you examine any.run’s terms of service: https://any.run/terms.pdf you’ll see today they are HQ’s in UAE (Funny enough any.run’s legal address up until October was Russia):
- “ANY.RUN” shall mean ANY.RUN LLC is the owner of exclusive intellectual property rights on the SaaS offered through the Website. Legal address of the ANY.RUN LLC is 432017, 10 Svobody Str., Ulyanovsk, Russian Federation. Detailed information is available upon request: support@any.run.
Myth 7: Avanan Requires More SOC Intervention not less
Myth: “Their [Avanan’s] Abuse Mailbox requires manual remediation which burdens SOC analysts. Desperate API Vendor’s Abuse Mailbox remediation is fully automated.”
Truth: This also requires a multipart response:
- The “Detect and Remediate”/”Post Delivery” approach that this Desperate API Vendor pushes is a game of “SOC Whack-a-Mole”. See “Whack-a-Mole” explanation at the bottom. This eats up cycles and creates confusion in the SOC.
- Avanan offers a full email incident response solution called IRaaS which is deployed as an additional service. According to one customer that recently evaluated both Avanan and the Desperate API Vendor in question, “Avanan offers a managed service (IRaaS) to respond to reported email. [Desperate API Vendor] does not.”
- Like every email security vendor, there is automation built into the product to ease service burdens. Automation is table stakes. What we offer is a FULL SERVICE with real people and an SLA. There is a massive difference between automation and a full service.
Customer quotes - Avanan vs. Desperate API Vendor Bakeoff
“Avanan offers a managed service (IRaaS) to respond to reported email. [Desperate API Vendor] does not.”
“[Desperate API Vendor] does integrate with Any.Run sandbox and Avanan does not integrate with a third party sandbox.” -
“[Desperate API Vendor] only analyzed email post-delivery. Although it was stated that malicious email that was delivered would be removed in milliseconds, it was determined to take longer in some tests performed by 15 – 30 minutes.”
“Avanan’ s mail explorer: Mail explorer offers advanced search filters including Date-hour, subject, sender, URL in body, sender display name, quarantine state, sender client IP, MD5, recipient, sender domain, server IP, headers. Allows rule creation for blocking/allowing an email on any of those search criteria. In addition to Avanan’s more advanced search fields, rule creation, and email retention period the ability to search for and download both malicious and clean emails made it stand out in this use case.”
“Overall Avanan gives us the feeling it is better designed to handle an organization of our size. There are additional features included that our organization would benefit from such as DLP, App security, Anomaly detection, and Shadow IT. The dashboard was intuitive and easy for our small team to manage and there is REST API for integration with our other tools.”
Check Point Sandblast vs. Any.Run
When it comes to malware sandboxing, zero-day malware analysis, Check Point Sandblast is the leader, blocking millions of attacks per day. Compare that to any.run that is just a few thousand. It’s not even in the same league.
|
Desperate API Vendor Sandboxing (Any.run) |
Check Point’s Sandboxing |
|
<5000 attacks detected in past 24 hours from four countries |
Check Point detects over 50M attacks per day globally in 88 countries |
SOC Whack-A-Mole
>Which type of solution has a lower impact on the SOC? Let’s compare the two types of solutions. One is the Avanan solution in Protect Mode and the other are the other API vendors that responds post-delivery.
|
Avanan in Protect Mode SOC Workflow |
Desperate API Vendor SOC Workflow |
|
|