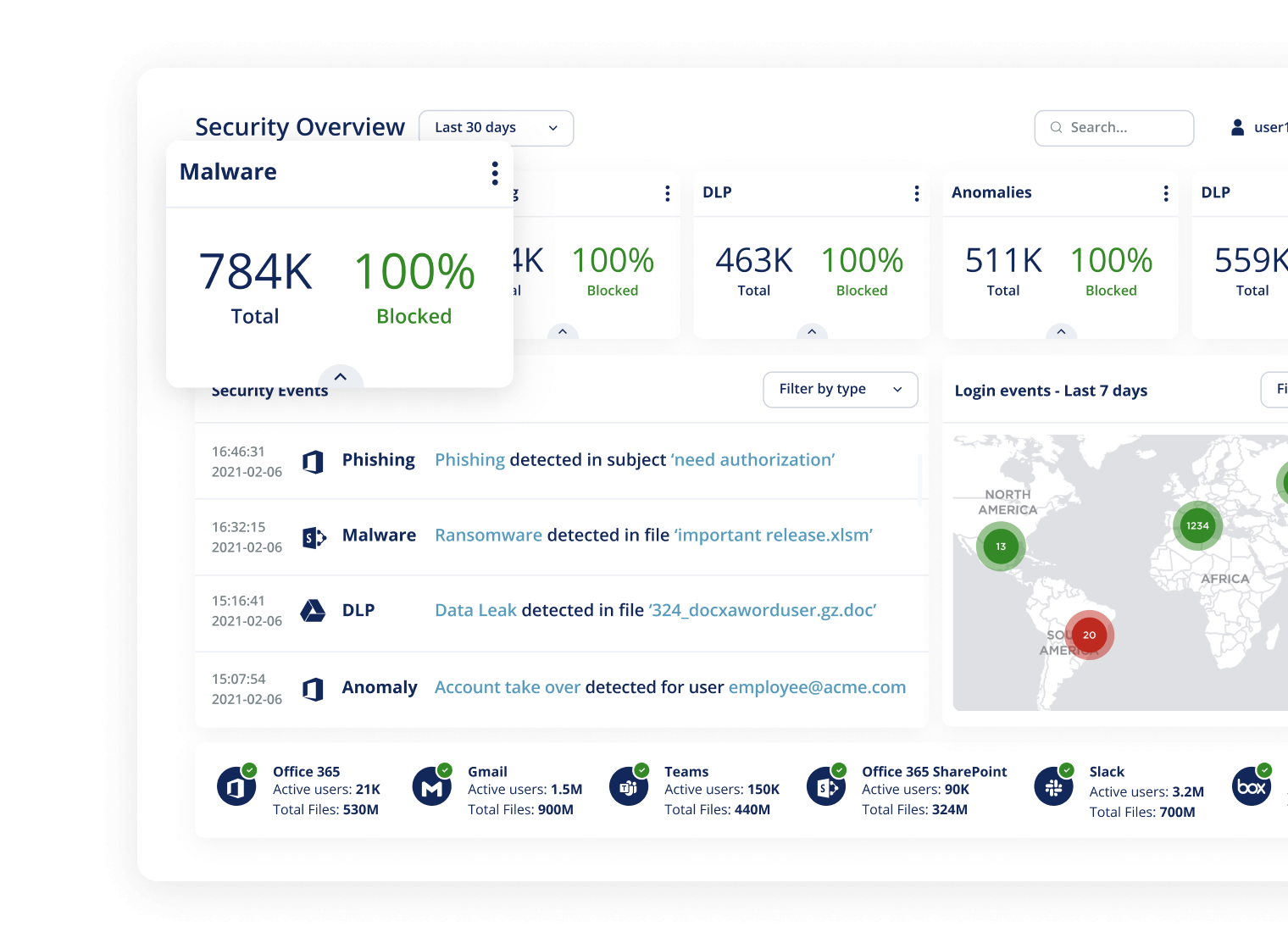
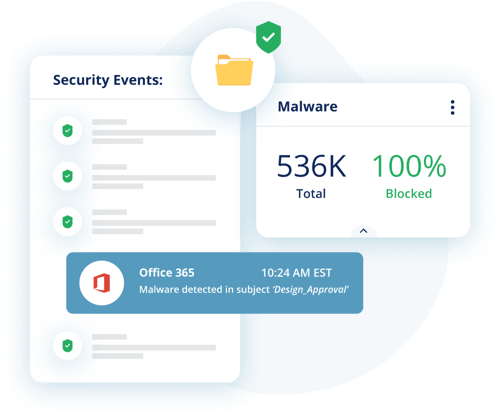
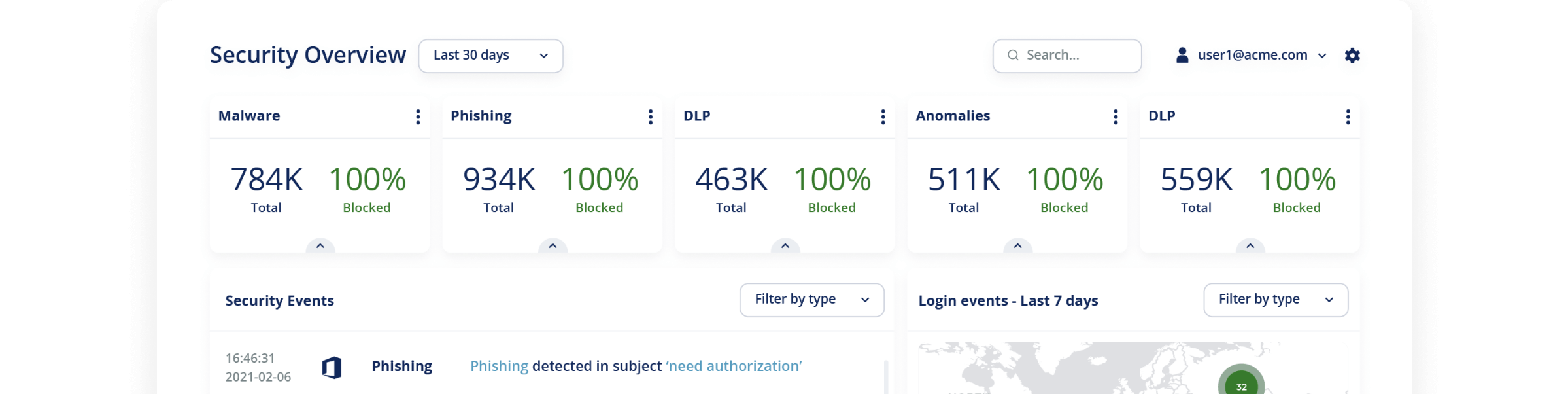
Protect your enterprise against zero-day malware and ransomware attacks.
Stop Phishing. Stop Ransomware
More than 75% of ransomware starts via email. By preventing malicious threats from reaching the inbox, Avanan protects your email from devastating ransomware.