Gmail Phishing is the most popular way for attackers to gain access to your Google Cloud. It can be difficult to keep up with all the methods for detecting phishing attacks on your own as the attacks get increasingly sophisticated every day.
That is why there are technologies (like Avanan) that detect and block phishing attacks for you.
If you are not employing an API based anti-phishing solution yet, you and everyone in your organization should know how to identify phishing attacks on your own. Although there are many lists of things to look for to find suspicious and malicious emails, many of their tips, such as looking for typos or incorrect logos, have grown obsolete as hackers have improved their techniques. These five checks are crucial for organizations to implement if they are looking to detect impersonation and malicious link based phishing attacks.
If you are looking for a software solution that will do these checks for you and more skip to the last section of this article.
1. Look beyond the display name
It is easy to set your display name to anything you want.
/1-Phishing-Bill-Gates.png?width=626&name=1-Phishing-Bill-Gates.png)
In Gmail, an easy way to the actual sender’s actual email address is to simply hover over their name without opening the email.
/2-Phishing-Bill-Gates.png?width=508&name=2-Phishing-Bill-Gates.png)
The example in the images above is much less sophisticated than the average attack. Often times an attacker will use an email address that looks much more legitimate. For instance an email from deliveries@ups.com may instead come from deliveries@alerts-ups.com or deliveries@ups.co. Which brings us to our next check.
2. Test the sender’s URL
The first URL you should check is the email host. For example, a package delivery notification may come from deliveries@alerts-ups.com. You can open up an incognito window (cmd + shift+ n in chrome) and check if alerts.ups.com is an actual website.
/3-Phishing-Test-Sender-URL.png?width=467&name=3-Phishing-Test-Sender-URL.png)
Oftentimes phishing attacks may come from what appear to be other users at your organization. Look closely for subtle typos in the sender’s domain, changing a .com to a .co or a .net is a common technique used by attackers. However, even legitimate email addresses can be falsified, in which case there are other URLs you need to check.
3. Test the URLs within the email body
Malicious URLs are the most popular form of phishing attack. A legitimate looking URL within the email will trigger download of malware or take you to a site designed to harvest your credentials.
/4-Phishing-Update-PW.png?width=503&name=4-Phishing-Update-PW.png)
You do not test a link by clicking on it, or opening it in a new window as you do not know what that link may trigger. In Gmail, you can hover over the link to reveal its actual destination.
/5-Phishing-Update-PW.png?width=544&name=5-Phishing-Update-PW.png)
Another method is to right click on the link and select “copy link address” and then paste it into a word document to view it safely.
/6-Phishing-Copy-Link-Address.png?width=466&name=6-Phishing-Copy-Link-Address.png)
If you can not determine the URLs legitimacy from the word document, you can enter the URL into a known phishing verification checker such as phishtank.com, which will let you know if the URL leads to a known phishing site.
/7-Phishing-PhishTank.png?width=462&name=7-Phishing-PhishTank.png)
4. If the sender is at your organization, contact them out of channel
A common method for spear-phishing attacks is for the attacker to send an email that looks like it is coming from an executive at your organization asking for login information or a wire transfer of funds. These usually present some sense of urgency in an attempt to convince the recipient to skip proper due diligence.
/8-Phishing-CEO.png?width=602&name=8-Phishing-CEO.png)
An easy way to check these is to call the sender on the phone, send them a message in Slack, or swing by their office to speak to them in person about the email in question.
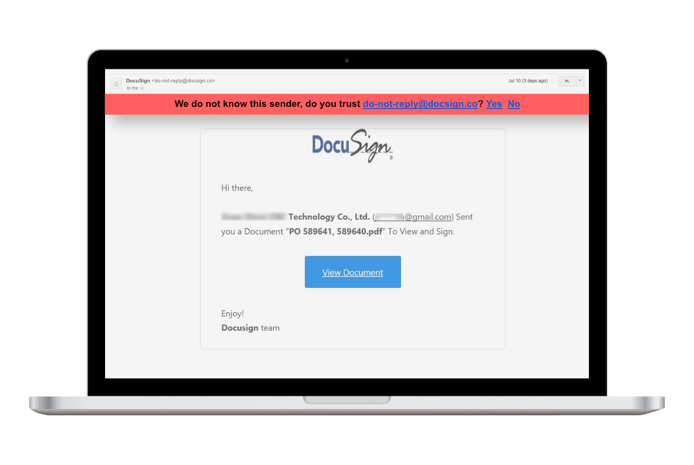
5. Avoid attachments
Without using additional security software (as described in the last section) there is no way to manually ensure an attachment is safe to open. Even seemingly innocuous files such as PDFs or Google docs can contain scripts that distribute malware across your cloud.
The only safe attachments are those that have been scanned by file sanitization software, otherwise your best bet is to use the tactic from #4 and contact the sender through another channel to verify they sent the attachment and what the attachment contains.
Conclusion
In the absence of an anti-phishing software, every user in your organization must complete all these steps for each email. No single step on its own is enough to verify an email’s legitimacy.
Even, with all these steps, phishing attacks are getting increasingly sophisticated in their effort to subvert detection and bypass these types of checks. An example of such an attack is the Google Docs phishing attack targeting Gmail users that impacted millions of users on May 4, 2017. When it comes to corporate email accounts we recommend using a security tool designed specifically for anti-phishing which will both detect and block malicious emails, saving you time and peace of mind.
Anti-Phishing Software
The Avanan Anti-Phishing package employs multiple strategies to catch phishing attacks targeting your Gmail domain as well as phishing attacks perpetrated through other SaaS applications. Employing anti-phishing tools from BitDefender, Checkpoint Sandblast, and our proprietary anti-phishing tool, Smart-Phish, simultaneously ensures that attacks designed to surpass a particular defense method will face more than one wall of security.
Avanan’s anti-phishing tools use a combination of impersonation analysis, URL and File analysis, and AI baselining to detect for suspicious activity to detect and quarantine phishing that even the most rigorous manual checks would miss.
If you are interested in learning more about how Avanan can protect your organization from phishing attacks click here to set up a demo and one of our security experts will contact you for a personalized walk through.






